Recently we wrote about the now-famous hack of a Jeep Cherokee. At Black Hat USA 2015, a large security conference, researchers Charlie Miller and Chris Valasek finally explained in detail, how exactly that hack happened.
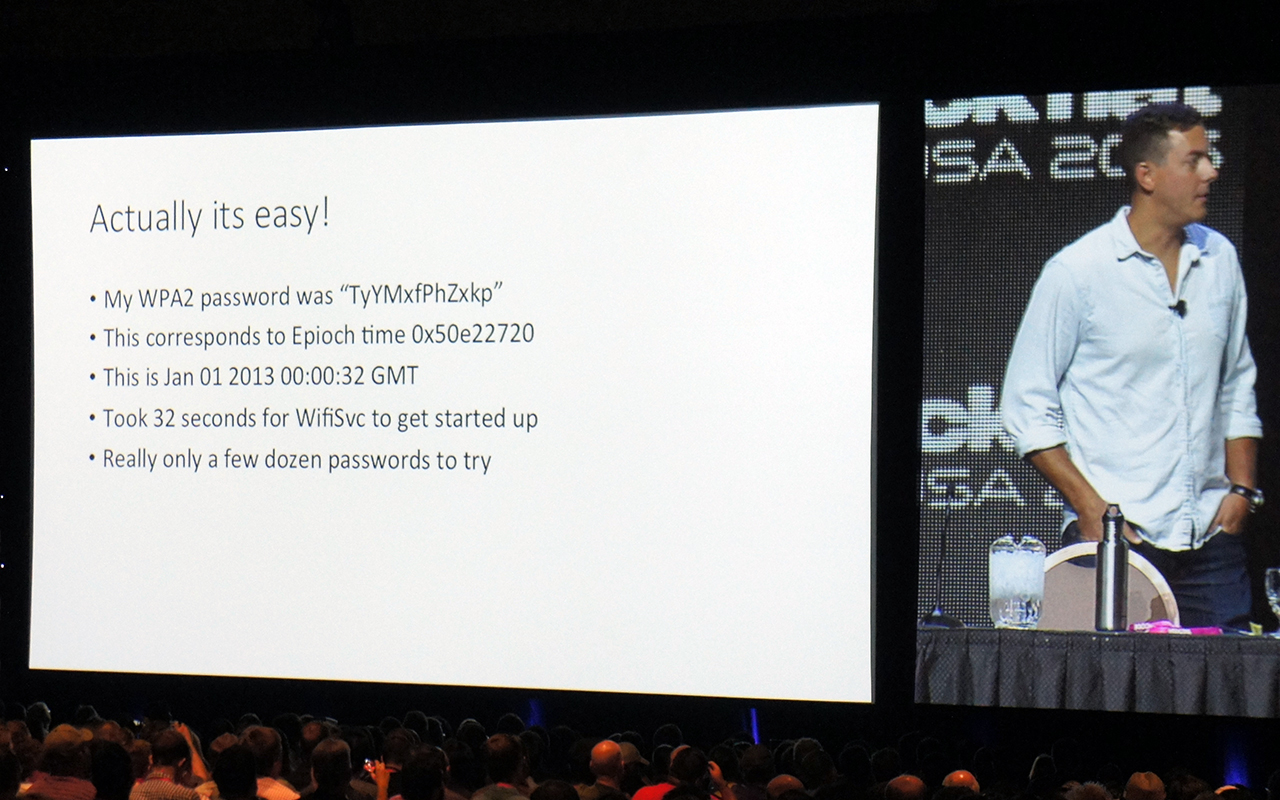
At the start of their research Miller and Valasek tried to hack the multimedia system of Jeep through Wi-Fi connection — Chrysler, the manufacturer of the vehicle, offers this option by subscription. It turned out, that it isn’t that hard to hack this Wi-Fi due to the fact that the Wi-Fi password is generated automatically, based on the time when the car and it’s multimedia system — the head unit — is turned on for the very first time.
In theory, considering the second precision of the date/time, it’s a rather secure method which gets you lots of possible combinations. But if you know the year when the car in question was manufactured and if you successfully guess the month you can bring the count down to just 15 million combinations. If you suppose the time was during the day, it gets you to about 7 million combinations. For a hacker, this number is pretty workable — you can brute force it within an hour.
Shock at the wheel: your Jeep can be hacked while driving down the road https://t.co/40h8StaLFG pic.twitter.com/bOvjzQb9K4
— Kaspersky Lab (@kaspersky) July 23, 2015
The problem is, that you need to follow that very Jeep for that hour to stay in touch with its Wi-Fi connection. The researchers tried to find another way. And — surprise, surprise! — they found one: it turned out, that the Wi-Fi password for Chrysler’s cars is generated before the actual time and date is set and is based on default system time plus a few seconds during which the head unit boots up.
So the January 01 2013 00.00 GMT it was, or more precisely 00.00.32 GMT in this very case. The number of combinations is very small, and it’s a piece of cake even for amateur hacker to guess the right one.
After connecting to the Jeep’s head unit, Miller and Valasek were able to find a possible way to hack the multimedia computer, which runs on a Linux operating system. Exploiting some pretty guessable issues in the software, they finally took control over the head unit’s system.
Possibilities of this hack are limited, but quite impressive: researchers were able to completely control the music player, set the radio to whatever station they wanted and its volume to any level. Imagine what can happen if someone is driving on 70 mph speed and suddenly his music changes to loud static.
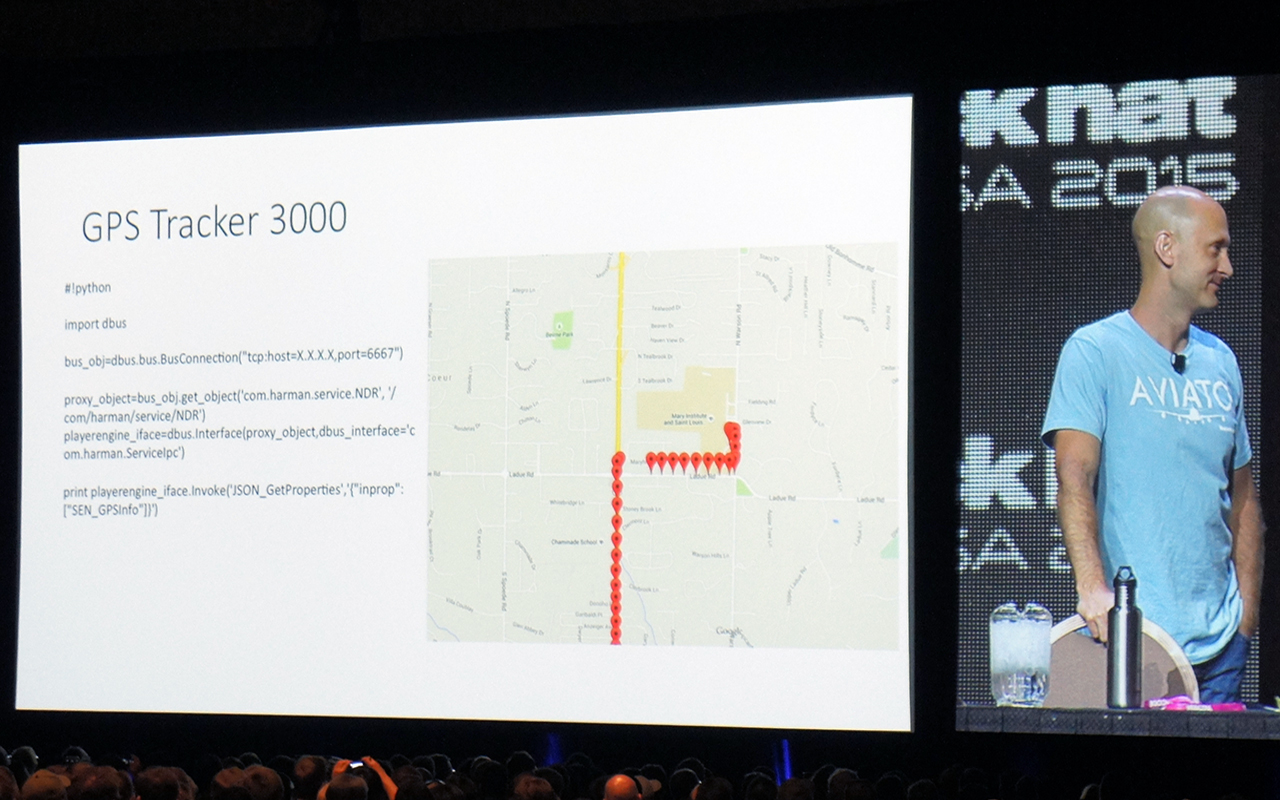
Another possibility researchers found is to track the car with its GPS navigational system. To exploit this possibility you even don’t need to change the head unit’s software, it’s a built-in option.
This is how to hack Wi-Fi connection of the Chrysler’s car if its owner is paying for the subscription. But currently there are not a lot of people who pay for this service. On the other hand, all of the head units are connected to Sprint cellular network, even if their owners have not purchased any wireless service. It’s just a standard for the automobile’s type of head units.
Miller and Valasek tried to exploit this way — it took a lot of time and efforts, but these efforts weren’t fruitless. With help of ‘femtocell’ (compact cellular base station) which they bought on eBay, they were able to get into Sprint internal network and manage a mass scan of IP addresses listening to the certain calls they already knew about after hacking through Wi-Fi.
Recall Alert: Fiat Chrysler is recalling 1.4 million hackable vehicles. Check affected cars: http://t.co/sErJGgCxqL pic.twitter.com/8HuTxKYIY0
— CNNMoney (@CNNMoney) July 25, 2015
Employing this trick you can find all of Chrysler’s cars equipped with this kind of head unit. Over a million of them were actually recalled by Fiat Chrysler. After that all you need is to choose the right one. Funny thing is that it’s rather hard to do, “it’s much easier to hack all the Jeeps than the certain one,” as the researchers say.
However, picking the wanted Jeep is doable as well, thanks to the option of the GPS tracker. After that you can make all the tricks with multimedia system you want. But this is not the end though.
The next step was to find a way to access CAN bus. This bus is a vehicle’s internal network, which interconnects all of the vehicle most important components — engine, transmission, sensors and so on and so forth, almost everything you have onboard, since almost every part of the vehicle is electronically controlled nowadays.
#BlackHat USA 2015: The full story of how that #Jeep was hacked
Tweet
The multimedia system is not connected to CAN bus directly. This is the thing that all the manufacturers always refer back to when it comes to IT-security of cyber-physical systems: there is an isolation they say, the air gap between connected and physical parts of these systems.
As it turned out, this air gap is not that thick, at least in Chrysler’s cars. Despite the fact that multimedia system’s controller itself can’t communicate directly with CAN bus, it actually can communicate with another component which is connected to CAN bus, the V850 controller. He knows a guy, who knows a guy situation, simply put.
The V850 controller’s software was designed in some cautious way, making it possible to listen to CAN bus, but not to send commands over it. But you know, it’s a computer after all. And if there’s no capability you need out-of-the-box, you can simply add one by reprogramming the computer.

Researchers discovered an opportunity to change firmware of the V850 controller for their maliciously crafted version through the connection to multimedia system’s controller. This firmware ‘upgrade’ can be done without any checks or authorizations. Even if there was authorization, researchers have found a couple of vulnerabilities that make possible taking control over this V850 controller.
And that was it: after this move Miller and Valasek were able to send commands through the CAN bus and make every — every! — component of the car to do whatever they wanted. They were able to control steering wheel, engine, transmission, braking system, not to mention dull things like windscreen wiper, air conditioner, door locks and so on. Moreover, they were able to control all this things completely remotely, over the Sprint cellular network.
Thanks to everyone who came to our talk. I know there were lots of other cool talks at the same time. pic.twitter.com/2RSLHKYJuK
— Charlie Miller (@0xcharlie) August 6, 2015
The good news is that it took years for Miller and Valasek to make their research. And the main trick — learning how to manage CAN bus connected components of the car — still stays unexplained by them. It’s not like everyone can do all the stuff, that the researchers have done. The bad news is that impressive hacks like this one are pretty possible. And the impact is hard to overestimate.
Update: 10 August 2015 Valasek and Miller published their research via whitepaper
Source: kaspersky.com



