 Independent Israeli information security specialist Barak Tawily discovered and described in detail in his blog critical DoS vulnerability in WordPress CMS. The bug has received the ID
Independent Israeli information security specialist Barak Tawily discovered and described in detail in his blog critical DoS vulnerability in WordPress CMS. The bug has received the ID  CVE-2018-6389 and is dangerous for all versions of WordPress released in the last nine years (including the most fresh release 4.9.2).
CVE-2018-6389 and is dangerous for all versions of WordPress released in the last nine years (including the most fresh release 4.9.2).  In his article, a specialist explains that the problem is related to the operation of load-scripts.php, which is used to process user requests. The original load-scripts.php was created for the convenience of site administrators so that they can improve the performance of their resources by concatenating several JavaScript files together. At the same time, the WordPress developers did not consider it necessary to protect this functionality with any kind of authentication so that the script could work without a login. In fact, load-scripts.php was available to anyone.
In his article, a specialist explains that the problem is related to the operation of load-scripts.php, which is used to process user requests. The original load-scripts.php was created for the convenience of site administrators so that they can improve the performance of their resources by concatenating several JavaScript files together. At the same time, the WordPress developers did not consider it necessary to protect this functionality with any kind of authentication so that the script could work without a login. In fact, load-scripts.php was available to anyone. 


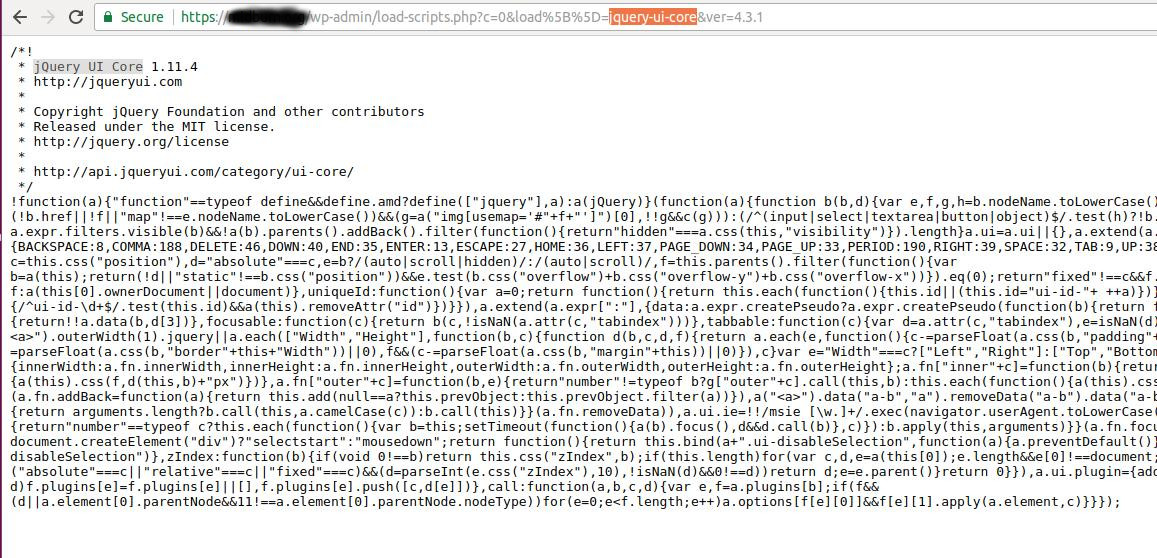
Depending on the installed modules and plugins, load-scripts.php selectively loads various JavaScript files, whose names are listed with a comma after the “load” parameter. That is, the URL should look like this:  https:/ /your-wordpress-site.com/wp-admin/load-scripts.php?c=1&load=editor,common,user-profile,media-widgets,media-gallery
https:/ /your-wordpress-site.com/wp-admin/load-scripts.php?c=1&load=editor,common,user-profile,media-widgets,media-gallery
 So, while the site is loading, load-scripts.php tries to find each of the JavaScript files listed in the URL in order to “give” them to the user's browser as a single file.
So, while the site is loading, load-scripts.php tries to find each of the JavaScript files listed in the URL in order to “give” them to the user's browser as a single file.  Tawaily discovered that an attacker could force load-scripts.php to load all possible JavaScript files at all by simply listing them in the URL. Because of this, the attacked site can start to work much slower, absorbing more and more server power. Of course, with a single such request, an attacker will not be able to provoke a denial of service, but the researcher created a proof-of-concept exploit: a simple doser.py script written in Python. The script sends many similar requests to the target URL. After about 500 requests, the average site running on a VPS server stops responding at all, “giving” only errors 502, 503 and 504.
Tawaily discovered that an attacker could force load-scripts.php to load all possible JavaScript files at all by simply listing them in the URL. Because of this, the attacked site can start to work much slower, absorbing more and more server power. Of course, with a single such request, an attacker will not be able to provoke a denial of service, but the researcher created a proof-of-concept exploit: a simple doser.py script written in Python. The script sends many similar requests to the target URL. After about 500 requests, the average site running on a VPS server stops responding at all, “giving” only errors 502, 503 and 504.
 The specialist notes that from one computer it is unlikely that it will be possible to “put” a working computer under managing a WordPress site located on a powerful, separate server, however, if the attacker has a wide channel or several bots at his disposal, the attack will work against such a resource, and it will turn out to be less costly for the attacker than a regular DDoS.
The specialist notes that from one computer it is unlikely that it will be possible to “put” a working computer under managing a WordPress site located on a powerful, separate server, however, if the attacker has a wide channel or several bots at his disposal, the attack will work against such a resource, and it will turn out to be less costly for the attacker than a regular DDoS.
 A video demonstration of the attack can be seen below.
A video demonstration of the attack can be seen below.
 Although DoS vulnerabilities are not covered by the WordPress bug bounty program, Tawaili still reported the problem to developers through the HackerOne platform. Unfortunately, the creators of WordPress did not consider the discovered vulnerability serious enough and said that such problems need to be addressed at the server or network level, but not at the application level. That is, there is no patch for this bug.
Although DoS vulnerabilities are not covered by the WordPress bug bounty program, Tawaili still reported the problem to developers through the HackerOne platform. Unfortunately, the creators of WordPress did not consider the discovered vulnerability serious enough and said that such problems need to be addressed at the server or network level, but not at the application level. That is, there is no patch for this bug.  In response To this, Barak Tawaily published his own fork of WordPress on GitHub, in which the vulnerability was fixed. Also, the researcher posted in the public domain bash-script, which allows you to fix the problem in existing WordPress installations . xaker.ru
In response To this, Barak Tawaily published his own fork of WordPress on GitHub, in which the vulnerability was fixed. Also, the researcher posted in the public domain bash-script, which allows you to fix the problem in existing WordPress installations . xaker.ru