Cryptocurrency mining is an IT industry buzzword and a rapidly growing phenomenon. As part of this far-reaching trend, more and more people take up “mining,” or adding blocks to a blockchain and getting rewarded for it with cryptocurrency. In doing so, these miners come up with more and more ingenious ways, not all of which are legal, to earn the coveted coins. And some of the more enterprising “miners” have no qualms about doing this at your expense.
Why miners need your computer
We have written before about botnets and how hackers can turn your computer into a zombie and make it a part of a botnet. A network of such zombie computers can be used for a variety of purposes, including but not limited to cryptocurrency mining.
In layman’s terms, your computer becomes a part of a distributed network whose computing power is used to mine a cryptocurrency that ends up in the botnet owner’s pocket. Several thousand computers on a botnet can mine cryptocurrencies much more effectively than a single computer can. In the case of a mining botnet, victims also foot the electricity bill, making installing miner applications on the computers of unsuspecting users a very lucrative business for hackers.
Note that a rank-and-file user can install a miner application intentionally, to mine cryptocurrency on their own. Distinguishing legal mining from illegal activity is the challenge. Miner applications are identical; the difference is in the covert installation and operation of illegally acting applications.
How a hidden miner ends up on your computer
In most cases, a miner ends up on a computer with the help of a purpose-built malicious application, a so-called dropper whose chief function is to secretly install another application. Droppers usually come under the guise of pirated versions of licensed products or activation key generators for them. Users look for this type of software on peer-to-peer networks and download it intentionally.
When the downloaded file is launched, an installer is deployed on the victim’s computer and in turn downloads a miner and a special tool that conceals it in the system. The application can also come complete with services that ensure its autorun and configure its settings.
For example, such services can suspend the miner when the user starts certain popular computer games. (The miner uses the computing power of the graphics card, and therefore, the game may start lagging and arouse the user’s suspicion.)
Such services can also attempt to disable antivirus products, suspend the miner when a system monitoring tool is running, and restore the miner if the user tries to delete it.
Scale of the problem
Hackers distribute such applications as a service. They use Telegram channels devoted to online work opportunities; you might come across ads offering trial versions of such droppers for distributing a hidden miner.
To give you an idea of the scale of this phenomenon: Our experts recently detected a botnet consisting of an estimated several thousand computers on which the Minergate miner was secretly installed. It mines not highly popular bitcoins but mostly those cryptocurrencies, such as Monero (XMR) and Zcash (ZEC), that allow the concealing of transactions and wallet ownership. The most conservative estimates reckon a single mining botnet can fetch more than $30,000 per month. More than $200,000 passed through the wallet used by the botnet our experts detected.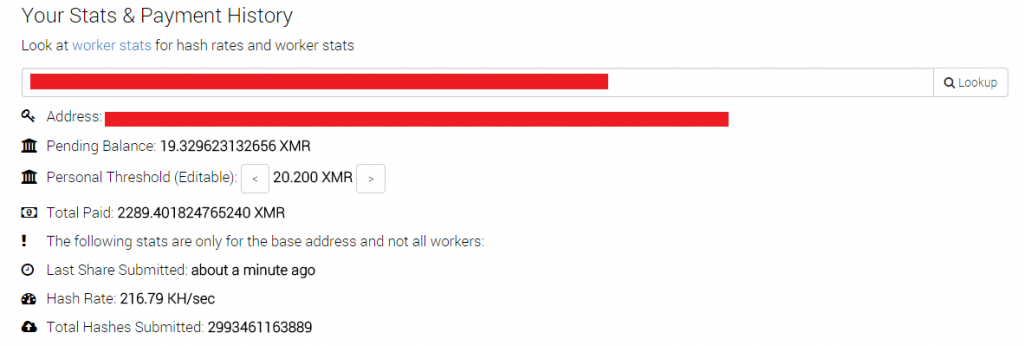
Monero wallet, used by criminals, mentioned above. Monero’s current exchange rate is about $120
How to protect yourself against this threat
Kaspersky Internet Security protects you against malicious droppers by default. Just make sure that your AV application is on at all times and this malware won’t stand a chance of infiltrating your computer. If for some reason you deactivate AV and run a manual scan after becoming suspicious, Kaspersky Internet Security will immediately detect this full-fledged Trojan and prompt you to get rid of it.
Unlike droppers, miners are not malicious applications, as we mentioned earlier. That’s why they fall into our riskware category — software that is legitimate but can be used for malicious purposes (you can find more details on what’s included in this category here). Kaspersky Internet Security does not block or remove such applications by default; a user may have installed them on purpose.
If you prefer to err on the side of caution and are certain that you won’t be using miners and other riskware, you can always open Kaspersky Internet Security’s settings, find the Threats and Exclusions section, and select the check box by Detect other software. Last but not least, scan your system regularly: Your security solution will help you avoid installing and running any unwanted applications.
Source: kaspersky.com




