Today, we are returning to our favorite topic of mobile solutions, or more accurately, the uninstallation procedure. There have been a number of inquiries on our corporate forum describing the following issue: a user, acting in accordance with the proper instructions, deletes our product, enters the secret code and then — wham! — his or her phone is blocked!
Moreover, it requires some PIN code. Understandably, the user sees an apparent correlation between this necessary ‘PIN’ and the Kaspersky product that they have just uninstalled, and then s/he attempts to enter the secret code again. But it won’t work. Perhaps the user thinks that they might have entered it incorrectly, and so they try to re-enter the secret code — again, with no success.
The root of the problem in this case is misinterpretation. In actuality, our product is no longer installed on the device as it was successfully deleted. This means that it is no longer responsible for protecting the device, and the lock screen has absolutely no relation to Kaspersky for Android. This is easy to understand by just looking at the buttons on the screen. The window that pops up, requesting the secret code, looks like this:
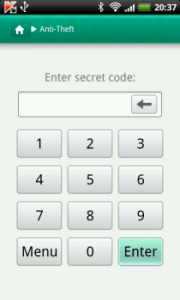
The design of the window corresponds to the overall design of the product and the buttons have only numbers on them. What is problematic for users might look like this:

In other words, it is a standard phone keyboard with numbers and characters with the regular wallpaper that is installed on the phone screen. One important detail should be taken into account when differentiating the two screens: in the first case, it is our product that requires the secret code; in the second case it is the device, which requires the PIN.
So what does this all boil down to? In the majority of cases, the entire situation likely has to do with some encryption software being installed on the device. Say you purchased a license key to our antivirus solution, installed Kaspersky Internet Security for Android, and then your security officers at work suggested that you also install, for example, KNOX.
The problem here is that our apps are not compatible with such programs. If you installed the encryption software prior to our product, our antivirus will notify you upon installation and ask that you delete that incompatible software. However, such notifications do not work in the opposite direction. It is likely that you will not know about this incompatibility issue in the first place, unless you delete our antivirus.
That’s essentially why it happens the way that it does. Upon activation of the Anti-Theft function, you must enter a secret code. Having encrypted the device again, with a newly installed encryption app, you will have a second password for your system, which will be responsible for system boots and home screen launches.
The last time Kaspersky Internet Security for Android will request the secret code is upon confirming uninstallation.
The last time Kaspersky Internet Security for Android will request the secret code is upon confirming uninstallation. After that, the product is removed and will stop working. Normally the system will stop asking for passwords and will reset those that were used before. However, this is not possible on encrypted devices — which is the source of the problem with a lock-up where you are required to enter your PIN.
So, what is the solution to this problem? There is a chance that you might be able to get into your phone by simply pressing Enter on the keyboard without entering any numbers. In some cases, the password to unlock the system is empty. If this does not work then the only other thing that you can do is what we call a ‘hard reset’ — resetting the device to its initial state.
Installing an additional #antivirus onto your device won’t make it safer, but instead it could lead to a major headache
Tweet
Once this process is done, you will then have to press a combination of buttons (depending on the model of the smartphone). This will erase all of the data stored on your device, including photos, contact lists and multimedia files. This is a very unfortunate occurrence, so we hope that you do not end up in this situation. To be on the safe side, we suggest that you regularly back up the data on your smartphone so that you will be able to retrieve your valuable content.
In closing, there is one idea that we should reinforce: installing additional antivirus solutions onto your device won’t make it safer, but instead it could lead to a major headache. The secret code for your Anti-Theft tool is reliable enough to keep your data well protected.
Source: kaspersky.com




