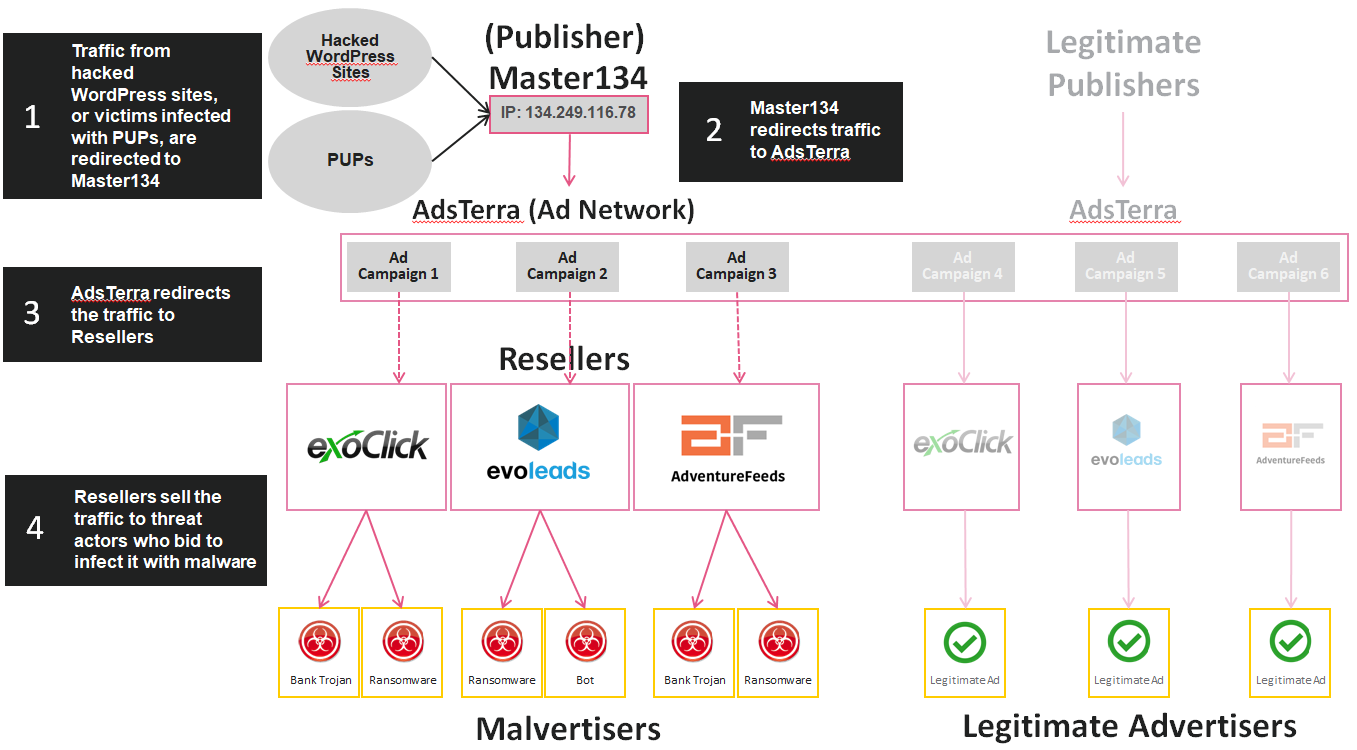
Check Point 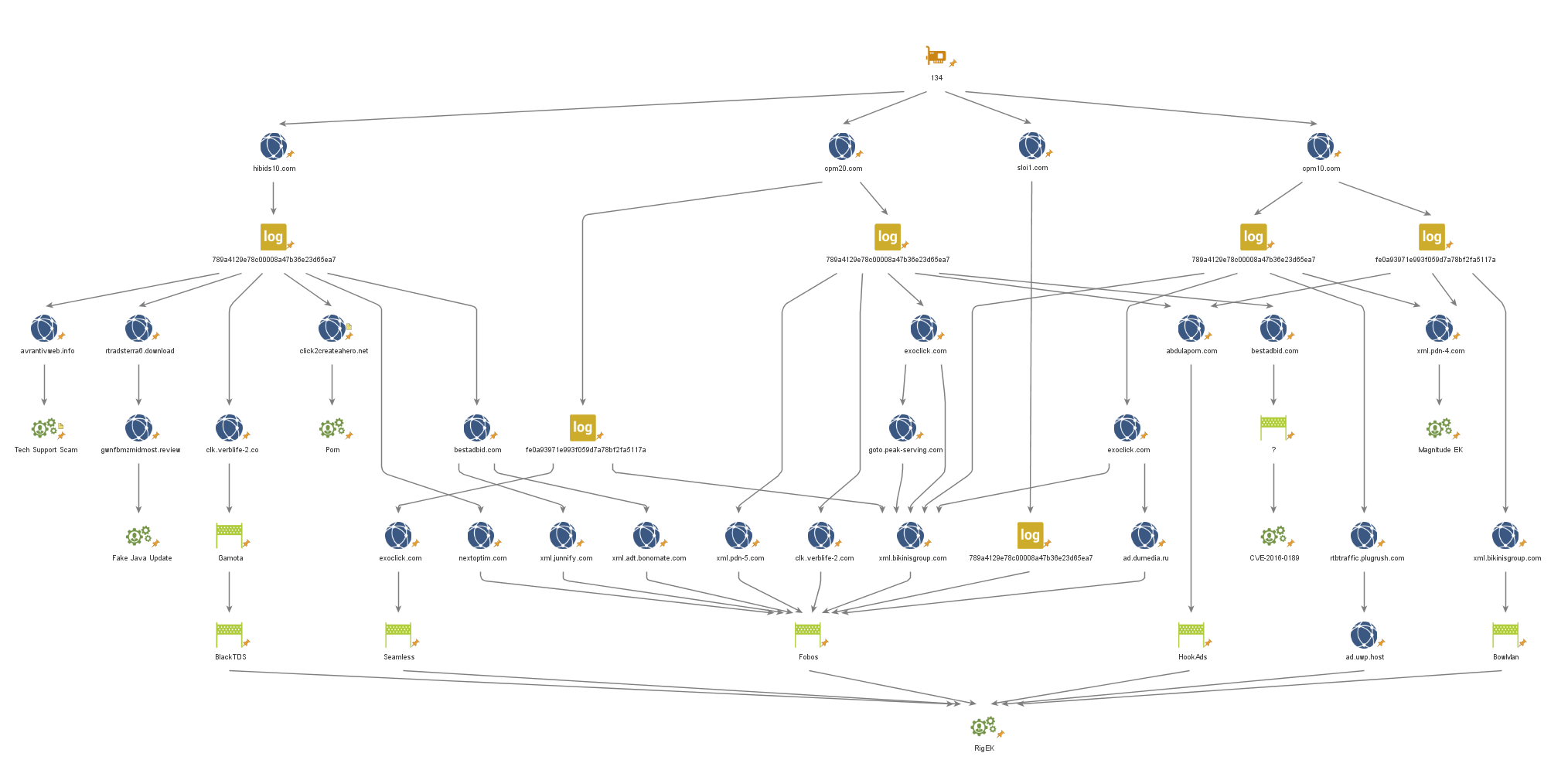 reported on the discovery a large-scale campaign to distribute malicious advertising. Over 10,000 hacked WordPress sites generate over 40,000 infection attempts every week. The researchers named the discovered scheme Master134, “in honor” of the attackers’ master server URL (134[.]249[.]116[.]78).
reported on the discovery a large-scale campaign to distribute malicious advertising. Over 10,000 hacked WordPress sites generate over 40,000 infection attempts every week. The researchers named the discovered scheme Master134, “in honor” of the attackers’ master server URL (134[.]249[.]116[.]78).
Scheme used by attackers
It all started when Master134 operators hacked over 10,000 WordPress sites. According to the researchers, sites on WordPress 4.7.1 were hacked – this version of the CMS is notorious for having an RCE vulnerability with which criminals can take control of the resource.
The attackers inject malicious code onto compromised sites, which is responsible for displaying ads to visitors and redirecting them to the “official” hacker redirect service. In addition, potentially unwanted programs (for example, software that changes the browser home page), which are also distributed by attackers, can also lead to the Master134 redirect portal.
The main way to monetize this entire system is to sell advertising slots. Thus, hackers place their offers in the large AdsTerra advertising network, on behalf of the Publisher account (“Publisher”) – such accounts are available to owners of sites that have free space for advertising. Then one of the three major resellers buys the advertising slots from the criminals: AdventureFeeds, EvoLeads or ExoClick. Experts write that then advertising space from resellers is bought by a variety of criminal groups. Thus, exploit kit operators (RIG, Magnitude, GrandSoft, FakeFlash), operators of traffic distribution systems (Fobos, HookAds, Seamless, BowMan, TorchLie, BlackTDS, Slyip), as well as numerous scammers and resource owners used the services of this ad reselling system through AdsTerra. fake technical support. Master134 ad chains: ad slots are sold through AdsTerra on behalf of the “Publisher” Check Point experts believe that all this is not a coincidence: criminals do not accidentally buy ad places and traffic exactly from the authors of Master134.
“It looks like there is some kind of large-scale collaboration between several groups of attackers at once, which is successfully supported through third-party advertising networks, the largest of which is AdsTerra,” analysts write.
Expe mouths believe that attackers pay for Master134’s services directly, and Master134’s operators, in turn, pay for the services of advertising networks, thus buying traffic redirection and, probably, even masking its sources.
“The the scenario makes Master134 a unique representative of the cybercriminal world. They generate advertising revenue by working directly with AdsTerra and successfully ensure that this traffic gets into the right (or rather “the wrong”) hands.”
 UPD. The first version of the report of specialists, among the resellers of advertising space intruders, was mentioned by the company AdKernel. Investigators later admitted that this was a mistake and that the company had nothing to do with the scam. Our material has also been corrected accordingly.
UPD. The first version of the report of specialists, among the resellers of advertising space intruders, was mentioned by the company AdKernel. Investigators later admitted that this was a mistake and that the company had nothing to do with the scam. Our material has also been corrected accordingly.




