Spam and phishing often go hand in hand: Fraudsters send mass mailings in an attempt to phish information from recipients. For them, users’ personal data remains a highly prized and desired asset, as evidenced by both the constant high-profile media stories and our own spam flow analysis. A common aim of spam is to gain access to your accounts or bank card numbers through e-mail phishing and social engineering techniques.
In this post, we look at the five tricks most commonly employed by spammers.
1. Fake notifications from social networks
Spammers actively send fake notifications that seem to come from popular social networks and are about new friends, their activities, comments, likes, and so forth. Such messages are often indistinguishable from the real thing, the only difference being that they contain a phishing link, which is not always easy to spot. On following the link, users are prompted to enter their username and password on a fake login page.
Another common variant is messages supposedly from social networks, but this time with threats alleging, for example, that suspicious activity has been detected on your account, or that a new feature has been introduced and users who don’t give their consent will be blocked. Whatever the case, the message will contain a button with a link to a phishing login page.
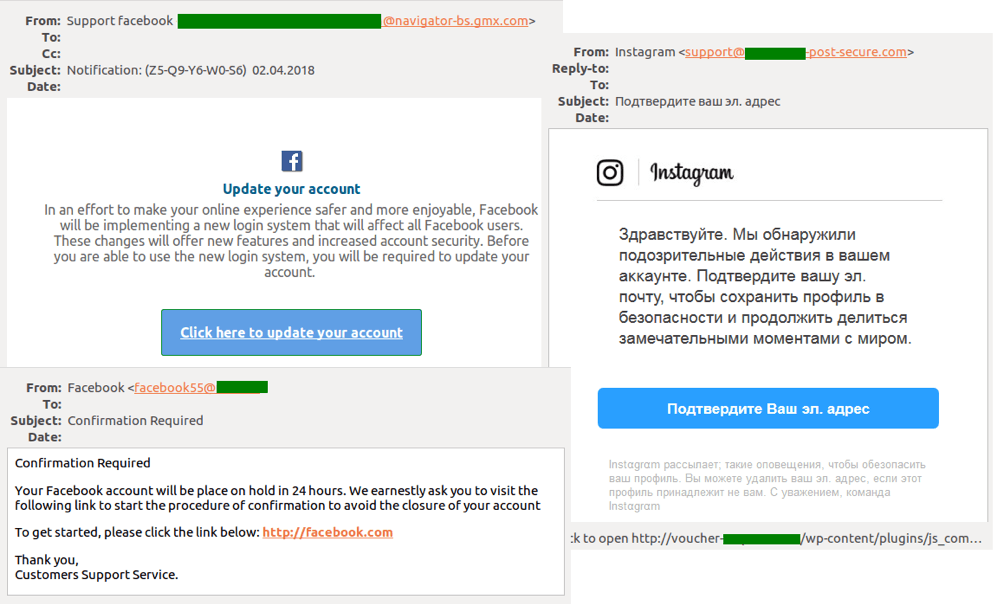
Phishers most popular tricks: Fake notifications from social networks
2. Banking phishing
Phishing aimed at obtaining users’ bank card details is still the most popular kind of fraud. Fake messages may be sent in the name of banks or payment systems. The most common message subjects are related to account blocking or “suspicious activity” on the client’s personal account.
Under the pretext of restoring access, confirming identity, or canceling a transaction, the user is asked to enter bank card details (often including the CVV/CVC code) on a fake bank website. On receiving the data, the criminals immediately withdraw money from the victim’s account. It’s the same story with payment systems, but in those cases, victims are asked only to log in to their accounts.
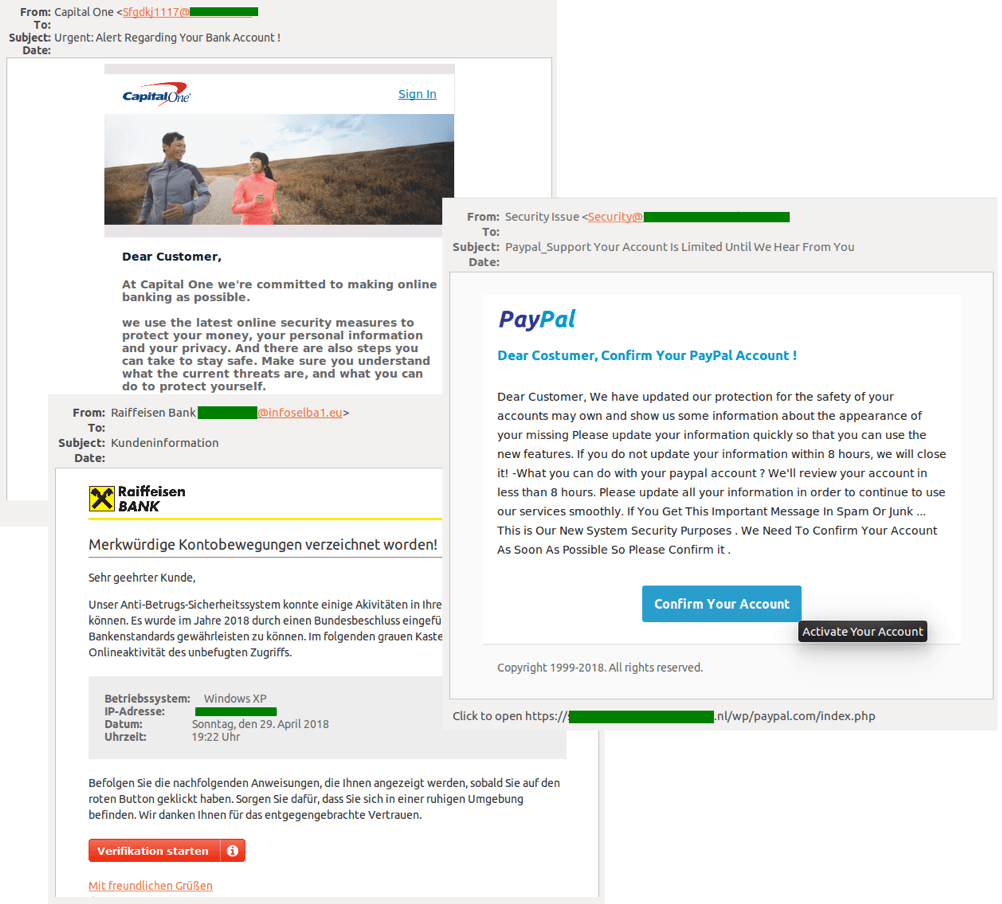
Phishers most popular tricks: Fake notifications from banks and payment systems
3. Fake notifications from popular services and sellers
Likewise, fake notifications are created using the brand names of popular online stores, delivery services, booking sites, multimedia platforms, job search websites, and other popular online services. Cybercriminals rely on the odds their spam messages will reach at least some genuine users of such services, who are likely to panic and click or tap whatever they see.
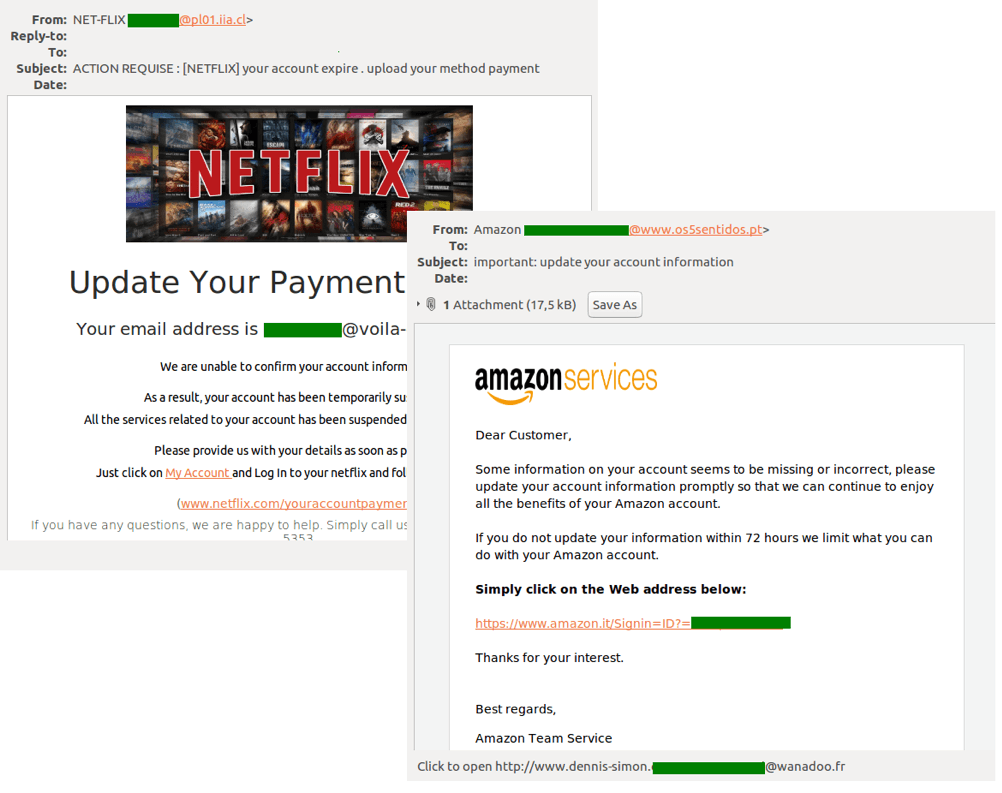
Phishers most popular tricks: Fake notifications from various services and shops
4. Fake notifications from e-mail services
Scammers use this kind of spam to harvest usernames and passwords for e-mail services. One of two common pretexts is typically deployed: Users are prompted either to restore their password or to increase the available space in their mailbox, which is supposedly full. In the latter case, the phishing link promises a manifold increase in storage capacity, which in the era of cloud computing and the ever-growing need for storing large amounts of data does not seem all that suspicious.
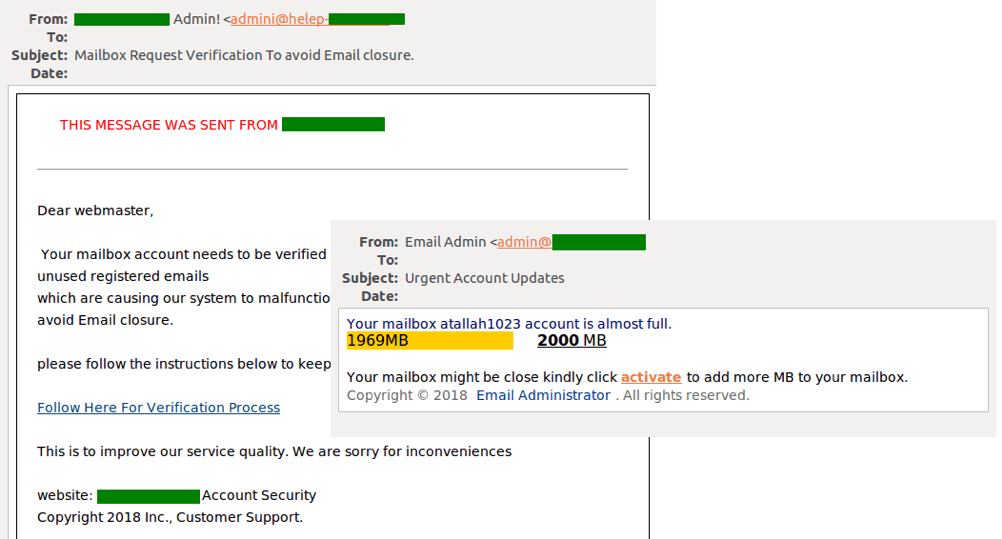
Phishers most popular tricks: Fake notifications from e-mail services
5. “Nigerian prince” fraud
Lastly, one of the oldest types of spam — the promise of fortune from a relative or a lawyer of a dead millionaire in exchange for an up-front payment — is still making the rounds. A variation on the theme involves the scammer posing as a celebrity in a difficult situation. Victims are promised an impressive reward if they agree to help the unfortunate millionaire withdraw funds trapped in various bank accounts. To do so, they must, of course, first send detailed information about themselves (passport details, account data, etc.) and a modest amount of money for paperwork.
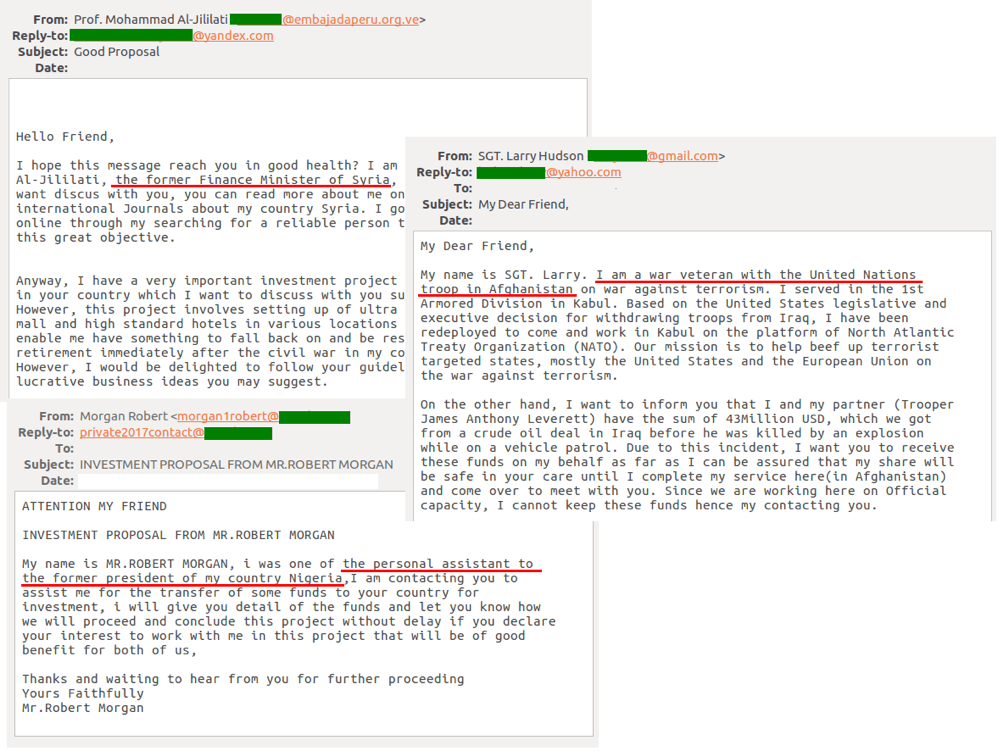
Phishers most popular tricks: Nigerian prince fraud
The list of spammers’ favorite topics and techniques does not end there, but the five methods described above are the most effective and thus the most common.
Don’t be a victim
The best advice is to be careful. But that’s a bit vague, so here’s some nitty-gritty:
- When you receive a message with a notification from a company or service, check that it was sent from a bona fide address. Using Google as an example, the message should come from no-reply@accounts.google.com, and not no-reply@accounts.google.scroogle.com or something like that.
- If you do follow a link in such a message, again, make sure that you are taken to the real website, not a fake.
- Use a reliable security solution with antispam and antiphishing protection — it will detect fraudulent e-mails and warn you clearly.
Source: kaspersky.com




