Company Analysts Defiant told about a dangerous vulnerability in the popular WP GDPR Compliance plugin. As the name suggests, this plugin is used to enforce the General Data Protection Regulation (GDPR). It helps to implement all the necessary notifications for users on the site and bring the resource in line with European standards.
About three weeks ago, attackers discovered a flaw in WP GDPR Compliance and started using it to inject backdoor scripts on vulnerable sites. But initially, messages about the compromise appeared on the support forums for another plugin. As it turned out later, this plugin was used on some hacked sites as a payload of the second stage of infection. And the source of the hacks, as mentioned above, was precisely WP GDPR Compliance.
Last week the WordPress developers were forced to remove WP GDPR Compliance from the official plugin catalog and only restored it a few days ago after the authors released the version 1.4.3, which fixed the problems.
However, Defiant experts warn that attacks are still ongoing. The fact is that many sites still work with plugin versions 1.4.2 and below, which means that they are still vulnerable.
A bug in WP GDPR Compliance allows attackers to access one of the plugin's internal functions and change the settings not only of the plugin itself, but of the entire CMS in general. There are currently two main attack scenarios. The first attack method looks like this:
- intruder exploits a bug to open the site's registration system;
- using a bug, it gives all new accounts the default administrator role;
- the hacker registers a new account, which automatically receives administrator rights (as a rule, this account is called t2trollherten);
- the attacker returns the default role for new accounts to the subscriber value and disables the registration of new users;
- the hacker logs into a new administrative account;
- a backdoor is installed on the site under the guise of wp-cache.php.
The backdoor contains a file manager, a terminal emulator and can run the PHP eval function, that is, it has everything necessary to upload additional payloads to the compromised site. 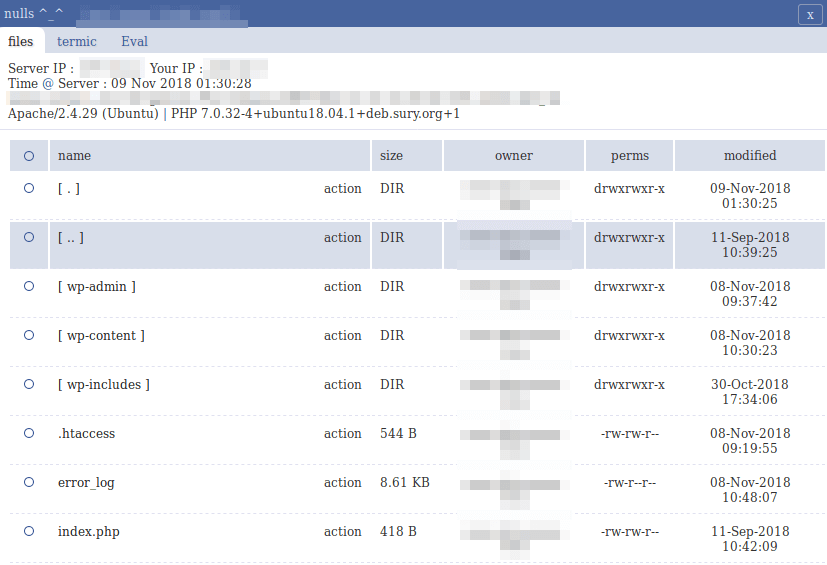
Second scenario The attacks, however, do not involve the creation of a new administrator account, which can be easily discovered by site owners. In this case, WP GDPR Compliance is used to add a new task to WP-Cron: download and install a 2MB Autocode plugin. With the help of this plugin, another backdoor is loaded onto the site (also disguised as wp-cache.php), slightly different from the one described above.
Although the second attack method was supposed to be more covert, it was Autocode that eventually drew users' attention to the problem, it was it that was initially considered the source of the problems, and it was thanks to this that Autocode was discovered gap in WP GDPR Compliance.
Source: xaker.ru




