There have been some stories about the kind of network air-gapping ordinary folks might see in spy movies or “Mr. Robot,” the point being that systems that have never been exposed to the Internet cannot have been compromised.
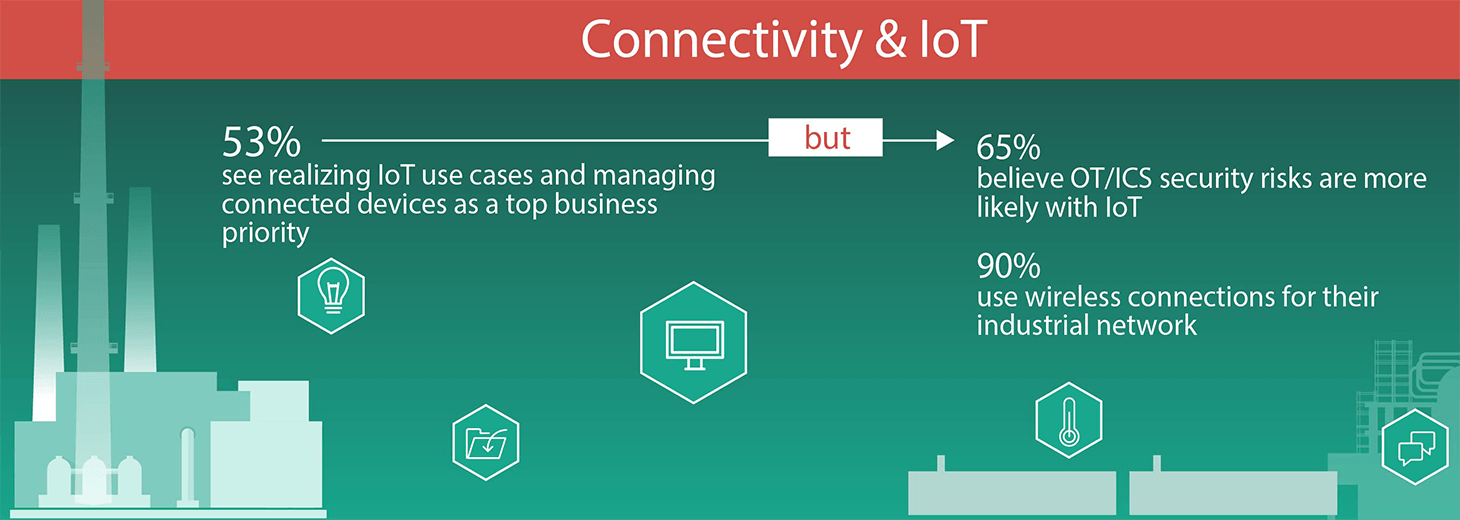
However, the “air-gap” concept isn’t the magic bullet it was once widely thought to be — but perhaps not for the reasons you might expect. According to our latest Industrial Control Systems survey, 90% of companies use wireless connectivity in their ICS environments — environments designed with the assumption that they would be used internally. But wireless connectivity increases the exposure of those industrial networks to the Internet — and to tons of malware intended to attack common computers.
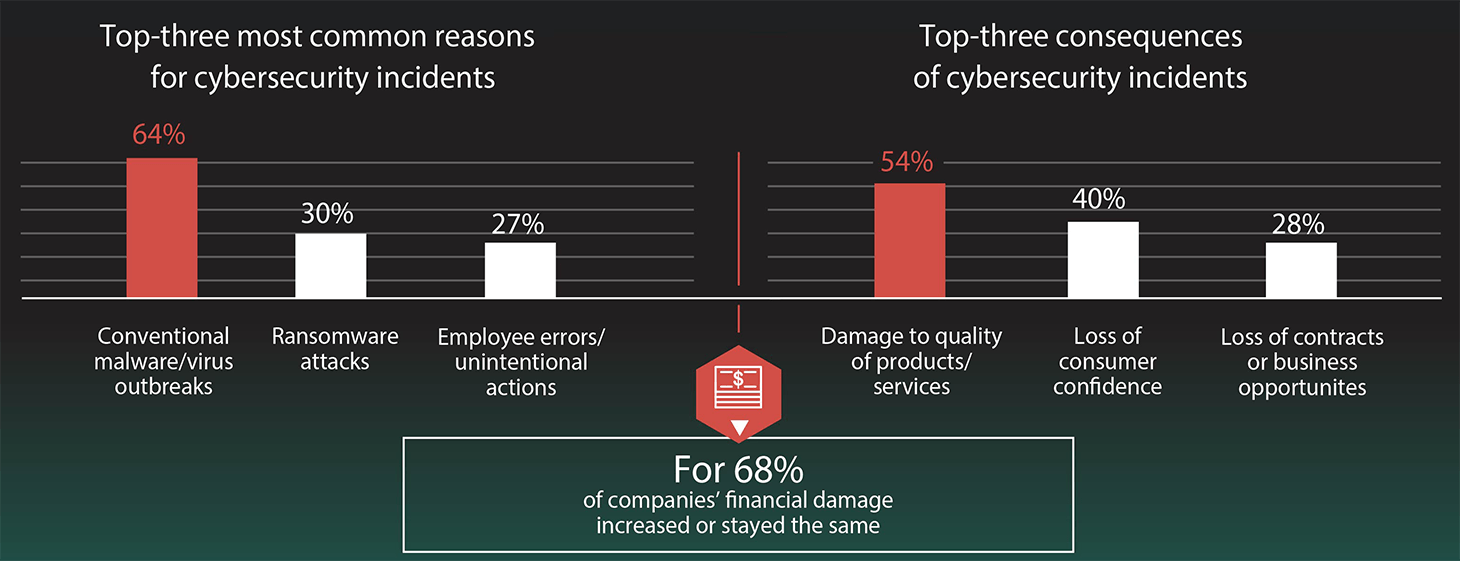
As a result, more than 40% of industrial companies registered at least one cybersecurity incident with operational technology, ICS or control system networks in the past 12 months. And almost two-thirds of them say that the cause of those incidents was conventional malware outbreaks. At least, those are results of the abovementioned survey, called “The state of industrial cybersecurity 2018.”
Of course, increased connectivity is only part of the problem. Consider the Forbes journalist who said he found 10 facilities working in the gas and oil industries using control systems that relied on outdated operating software. And knowing how conservative those industries tend to be about changing their software or processes in any way, we think it’s safe to say far more than 10 of them aren’t up to date.
Another part of the problem may be in the way they implement protective measures. Most of them use traditional antimalware and antivirus solutions in their office networks, but not in industrial ones. That’s understandable; they are afraid antimalware solutions would interfere with technological processes and cause more problems than they could possibly solve.
However, that does not explain another finding of our survey: Only 56% of companies implemented network monitoring and log analysis instruments for OT/ICS purposes. And 28% do not even understand the concept of performing regular vulnerability scanning.
Learn more about the results of the survey in our report, “The state of industrial cybersecurity 2018.”
Source: kaspersky.com




