Defiant experts that attackers are exploiting an XSS vulnerability in the plugin Abandoned Cart Lite for WooCommerce installed on 20,000 websites. This plugin allows administrators and other privileged users to view products “forgotten” by buyers, in cases where the user added the goods to the cart, but did not complete the purchase and for some reason left the resource. The data collected in this way, for example, can be used to generate a list of popular products and other analytics.
An XSS vulnerability exploited by criminals allows a product with a maliciously crafted name to be placed in the shopping cart. After that, the exploit of the attackers will be saved in the store database and will work as soon as this page is viewed on the backend. As a result, the exploit will access the short address bit.ly and upload JavaScript to the vulnerable site, which will infect the resource with two different backdoors.
The first backdoor creates a new user woouser with administrator rights, which is always registered using the mail [email protected], and its password is “K1YPRka7b0av1B”. The second backdoor is more elegant: it lists all the site’s plugins and searches among them for the first one that was disabled by the real administrator. Hackers do not re-enable this plugin, but replace its content with a malicious script. Although the plugin remains disabled, its files are still stored on disk, and therefore available for requests, and the second backdoor of the attackers can be activated, for example, if the victim detects an infection and deletes the woouser account.
According to researchers, bit.ly has been accessed more than 5,200 times so far, so there are, most likely, hundreds or even thousands of sites have already suffered from these attacks.
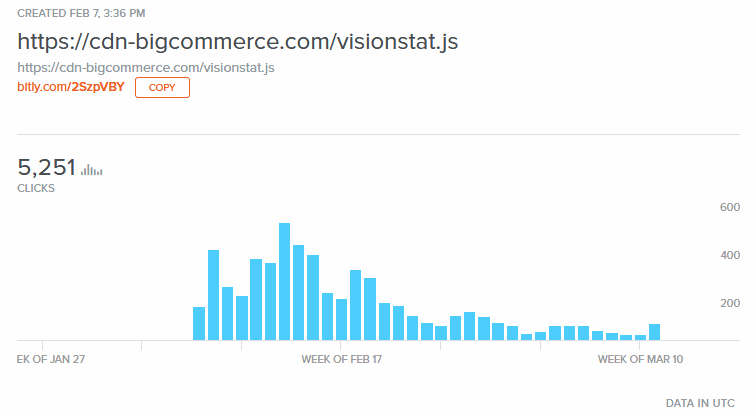 As you can see in the chart above, the peak of attacks occurred in mid-February 2019, but hacks are still ongoing. It is worth noting that back on February 18, the developers of Abandoned Cart Lite for WooCommerce released an updated version 5.2.0, where the XSS vulnerability was fixed. Defiant experts are reminding admins to keep plugins up to date and to check for suspicious new users like woouser on the site.
As you can see in the chart above, the peak of attacks occurred in mid-February 2019, but hacks are still ongoing. It is worth noting that back on February 18, the developers of Abandoned Cart Lite for WooCommerce released an updated version 5.2.0, where the XSS vulnerability was fixed. Defiant experts are reminding admins to keep plugins up to date and to check for suspicious new users like woouser on the site.
Source: xaker.ru




