Malware inflicts damage to your system, yet is ephemeral and rarely visible to the naked eye, especially in digital domains beyond your own PC. But nevertheless, you have an opportunity to see the scale and magnitude of the problem with your own eyes thanks to our map depicting malware epidemics in real time.
In today’s world, it takes minutes for new malware applications or spam to be distributed.
In today’s world, it takes minutes for new malware applications or spam to be distributed.
This is why all robust anti-virus software has long been using the Internet to study newly compromised files and the freshest threats as soon as they pop up. To find out more, you can read our article on the Kaspersky Security Network, but in the meantime we are going to tell you about the new and exciting ways you can use KSN data. We plot this data on a map of the world in real time so you have an opportunity to compare different kinds of threats and the ways they are distributed. Which country gets more spam in the morning: Germany or USA? Who more readily clicks on malicious links: Russians or Japanese? Which country leads in terms of malware infection rates? (Hint: the answer depends on the time of the day). All of it is available on our comprehensive cybermap (always available at kas.pr/war).
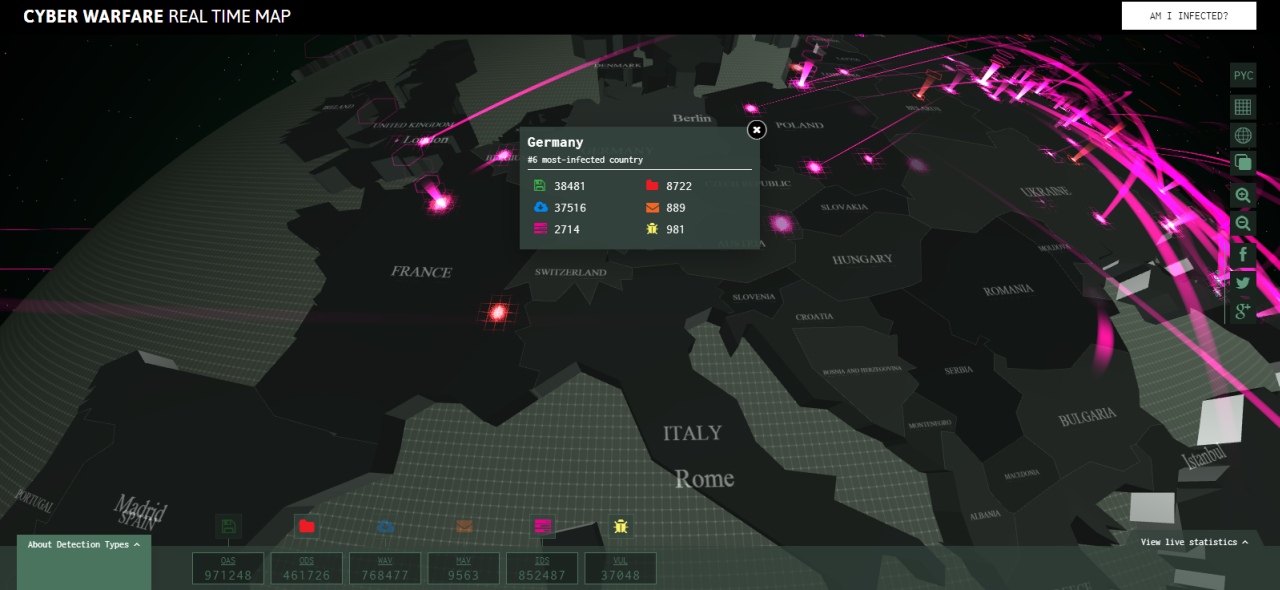
Now, a bit of background on how it functions. The globe spins with the help of your mouse, while the scroll wheel zooms in or out. Different types of threats are color-coded. The button in the lower left corner serves to provide a description of each threat (certain types of threats can be configured to be hidden for your convenience). The buttons to the right of the globe help to manage a view: besides a couple of necessary buttons, like ‘zoom’ and ‘share’, the panel includes three useful switches as well. One of the buttons changes color themes from ‘black’ to ‘white’, another allows you to change the language of the interface, and the third switches views between ‘globe’ and ‘2D map’ modes.
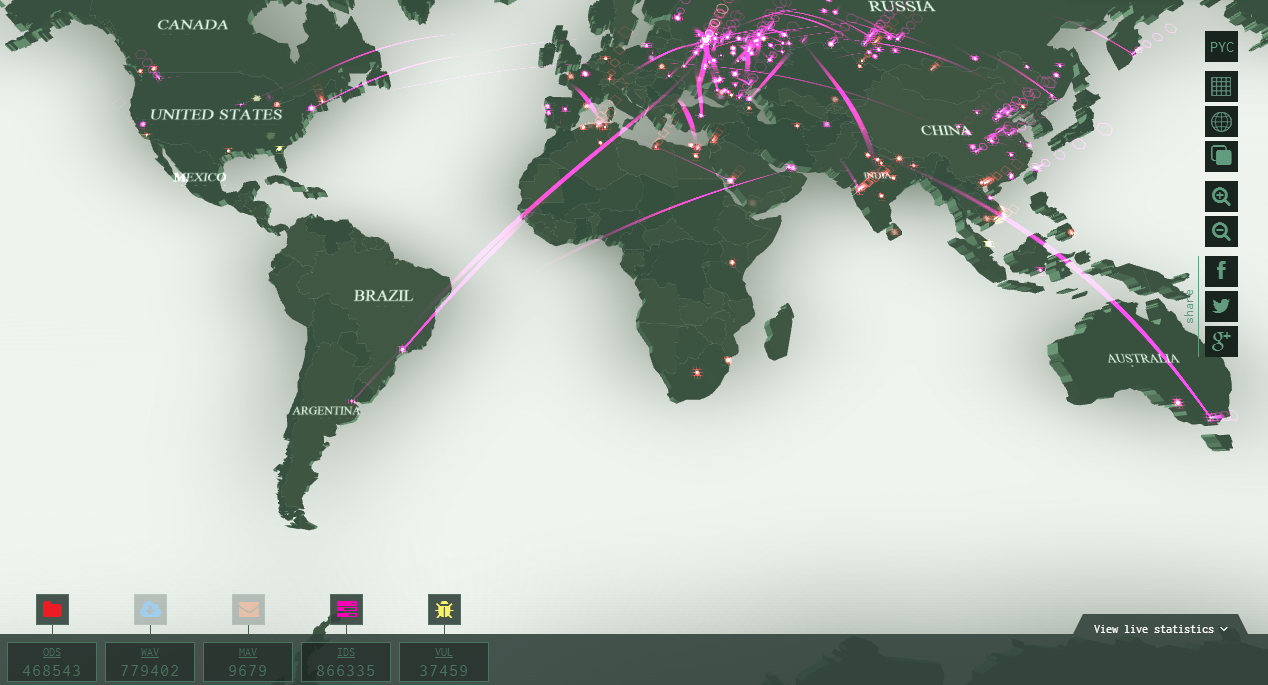
By clicking on a country, you will see the number of threats detected there since 12 a.m. GMT and the position the country holds in the world’s ‘malware affection’ rating. To see the list of top countries and a couple of useful graphs, use the ‘statistics’ button in the lower right corner.
The most useful button is located in the upper right corner. It helps to spare your system the miserable fate of contributing to the sad statistics on our cybermap. To check your PC for viruses free of charge and to prevent further exposure to malware, click on ‘Check my PC’ button.
Source: kaspersky.com



