Specialists from Defiant found a botnet, which already has 20,000 infected WordPress sites and brute-forces other WordPress sites using dictionary attacks. In the last month alone, experts recorded more than 5,000,000 such attempts to enumerate credentials.
According to the researchers' report, the botnet is controlled through four C&C servers, which issue commands to infected resources. C&C servers send instructions to sites using over 14,000 proxies rented from best-proxies[.]ru. 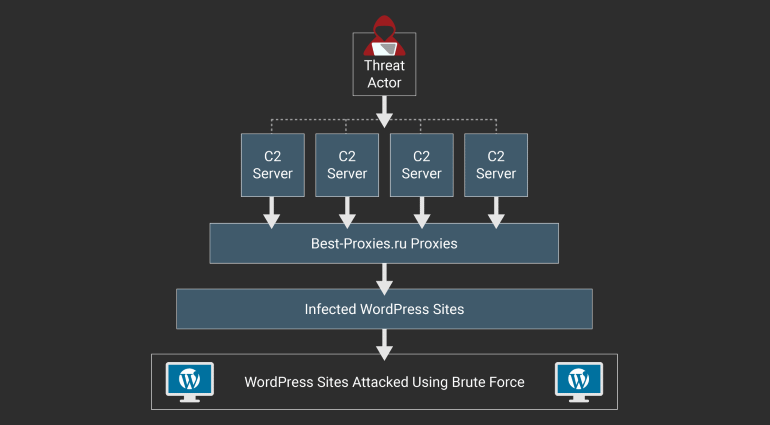 Botnet infrastructure Commands are sent to malicious scripts hosted on infected sites. These scripts receive lists of targets from command and control servers and prepare a list of possible passwords for them based on the list of password patterns. Then, using the resulting combinations, the scripts begin to brute-force the admin panels of the target resources.
Botnet infrastructure Commands are sent to malicious scripts hosted on infected sites. These scripts receive lists of targets from command and control servers and prepare a list of possible passwords for them based on the list of password patterns. Then, using the resulting combinations, the scripts begin to brute-force the admin panels of the target resources.
“If the brute-force script tries to log in to example.com on behalf of the user alice, it will generate passwords like alice1, alice2018, and so on . Although such tactics are unlikely to be successful against one particular site, they can be effective if used on a larger scale, against a large number of targets,” the researchers say.  Because to hide their activities Because the botnet uses numerous proxies, under normal circumstances, Defiant analysts should not have discovered its entire infrastructure so easily. However, it is reported that the operators of the malicious campaign “made a number of mistakes in the implementation of their brute-force scripts”, which allowed analysts to detect the backend and understand the botnet's operation model. In addition, analysts write that the botnet operators made a mistake in the implementation of their own authentication system in the admin panel. As a result, specialists were able to bypass the authorization system and observe the operation of the botnet from the inside. Researchers report that they have already handed over all the collected data to the hands of law enforcement agencies, but so far the botnet is still in service and continues to work. The fact is that it was not so easy to take his command and control servers offline – they are hosted by HostSailor hosting, which is positioned as “bulletproof”. It is not necessary to wait for the administration of such a hosting to respond to requests and take action.
Because to hide their activities Because the botnet uses numerous proxies, under normal circumstances, Defiant analysts should not have discovered its entire infrastructure so easily. However, it is reported that the operators of the malicious campaign “made a number of mistakes in the implementation of their brute-force scripts”, which allowed analysts to detect the backend and understand the botnet's operation model. In addition, analysts write that the botnet operators made a mistake in the implementation of their own authentication system in the admin panel. As a result, specialists were able to bypass the authorization system and observe the operation of the botnet from the inside. Researchers report that they have already handed over all the collected data to the hands of law enforcement agencies, but so far the botnet is still in service and continues to work. The fact is that it was not so easy to take his command and control servers offline – they are hosted by HostSailor hosting, which is positioned as “bulletproof”. It is not necessary to wait for the administration of such a hosting to respond to requests and take action.




