Wordfence specialists report that attackers have come up with a new way to compromise sites running WordPress. The attackers use poorly protected WordPress.com accounts and the Jetpack plugin to install plugins with backdoors on various websites.
According to researchers, a new type of attack has been used by criminals since May 16, 2018. This is also confirmed by posts by affected users on the WordPress.org forums.
At the first stage of the attack, hackers pick up a username and password (credentials are taken from various large leak databases) suitable for WordPress.com account. Since the problem of password reuse is still one of the main weaknesses of users, there is no shortage of such accounts for attackers.
It’s worth noting here that WordPress.com accounts are primarily used to manage blogs hosted on the Automattic platform, i.e. they are different from WordPress.org accounts or administrative accounts of individual sites under managing WordPress CMS.
However, a few years ago, Automattic developers presented to the public open source analytics plugin Jetpack, based on the version then used by WordPress.com. Now the open source version of this plugin has acquired many useful features and is widely used by administrators of stand-alone sites based on WordPress.
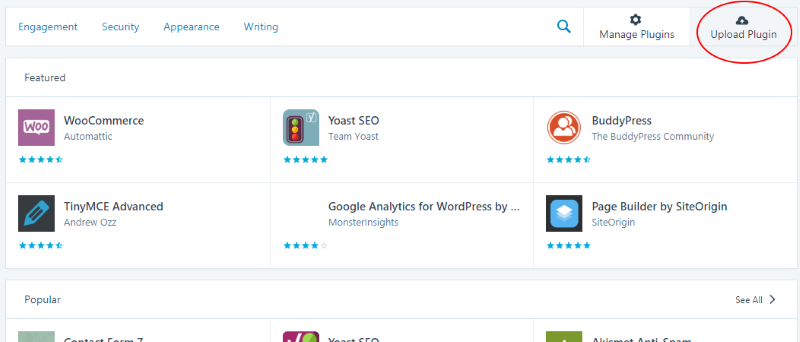
One of the features of the Jetpack plugin is the ability to link a single WordPress site to a WordPress.com account. Thus, the Jetpack panel can be used directly from under WordPress.com, and it can be used to simultaneously manage hundreds of WordPress sites from one place. To do this, of course, you need to install Jetpack on each site, but WordPress.com offers the ability to install Jetpack right from its control panel. At the same time, the plugin does not even have to be placed in the official WordPress.org repository, which gave attackers the opportunity to upload an arbitrary ZIP file containing malicious code to sites.
According to Wordfence, attackers are taking control of WordPress.com accounts, and if stand-alone sites running WordPress are linked to the account, criminals get the opportunity to install malicious plugins containing a backdoor on them. So, on May 16, unknown hackers distributed the pluginsamonsters plugin in this way, and on May 21 they switched to the wpsmilepack plugin. So far, attackers use such backdoors to send spam and create fake technical support pages.
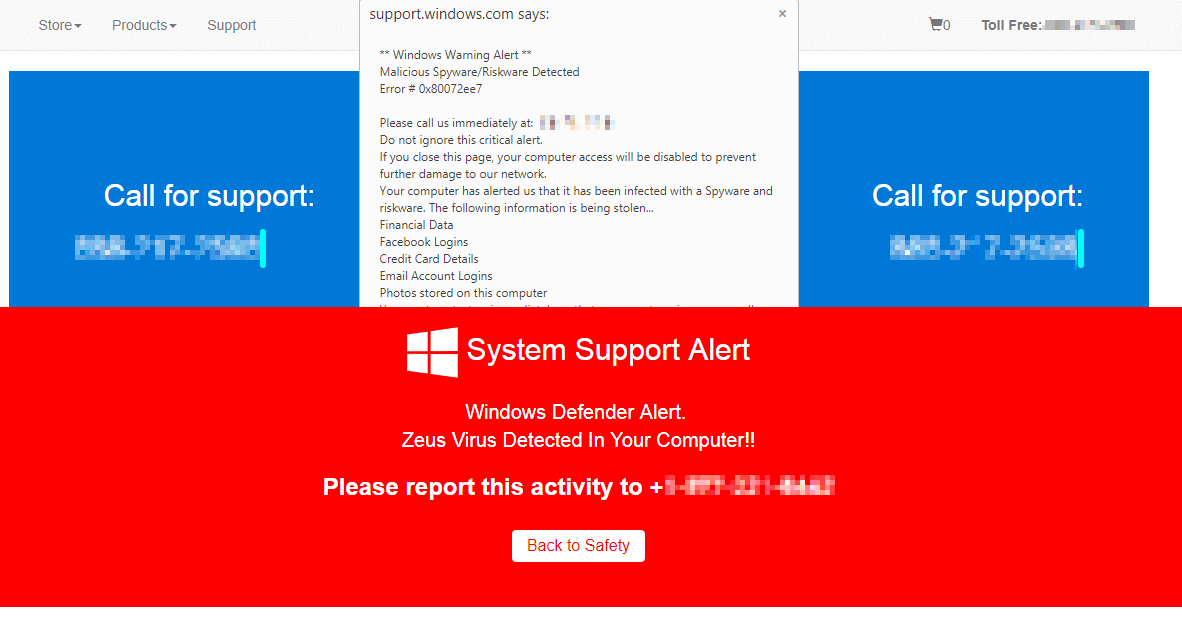 The exact number of affected resources is unknown, and the researchers note that even detecting such an attack is very difficult. The fact is that malicious plugins are visible in the WordPress.com control panel, but “invisible” in the list of plugins on the affected sites themselves. As a result, experts urge site owners who also have WordPress.com accounts to check the list of installed plugins and, if necessary, remove malicious solutions, change passwords, and enable two-factor authentication.
The exact number of affected resources is unknown, and the researchers note that even detecting such an attack is very difficult. The fact is that malicious plugins are visible in the WordPress.com control panel, but “invisible” in the list of plugins on the affected sites themselves. As a result, experts urge site owners who also have WordPress.com accounts to check the list of installed plugins and, if necessary, remove malicious solutions, change passwords, and enable two-factor authentication.