How to disguise your traffic as a website?
Every user who is concerned about their privacy uses traffic encryption technology. The most popular of them is
A VPN (Virtual Private Network) is used to provide staff are working remotely with secure access to the private network of a corporation or other organization, over the Internet. Encryption and other security features are used to maintain privacy and prevent unauthorized access to the private network.
” href=”https://10alert.com/glossary/vpn/” target=”_blank”>VPN
.
There is also a more advanced encryption technology – to disguise your traffic as a website.
A VPN (Virtual Private Network) is used to provide staff are working remotely with secure access to the private network of a corporation or other organization, over the Internet. Encryption and other security features are used to maintain privacy and prevent unauthorized access to the private network.
” href=”https://10alert.com/glossary/vpn/” target=”_blank”>For example google.com
.
On Android, you can do this using the program HTTP Injector:
1.
A VPN (Virtual Private Network) is used to provide staff are working remotely with secure access to the private network of a corporation or other organization, over the Internet. Encryption and other security features are used to maintain privacy and prevent unauthorized access to the private network.
” href=”https://10alert.com/glossary/vpn/” target=”_blank”>Run the program.
2.
A VPN (Virtual Private Network) is used to provide staff are working remotely with secure access to the private network of a corporation or other organization, over the Internet. Encryption and other security features are used to maintain privacy and prevent unauthorized access to the private network.
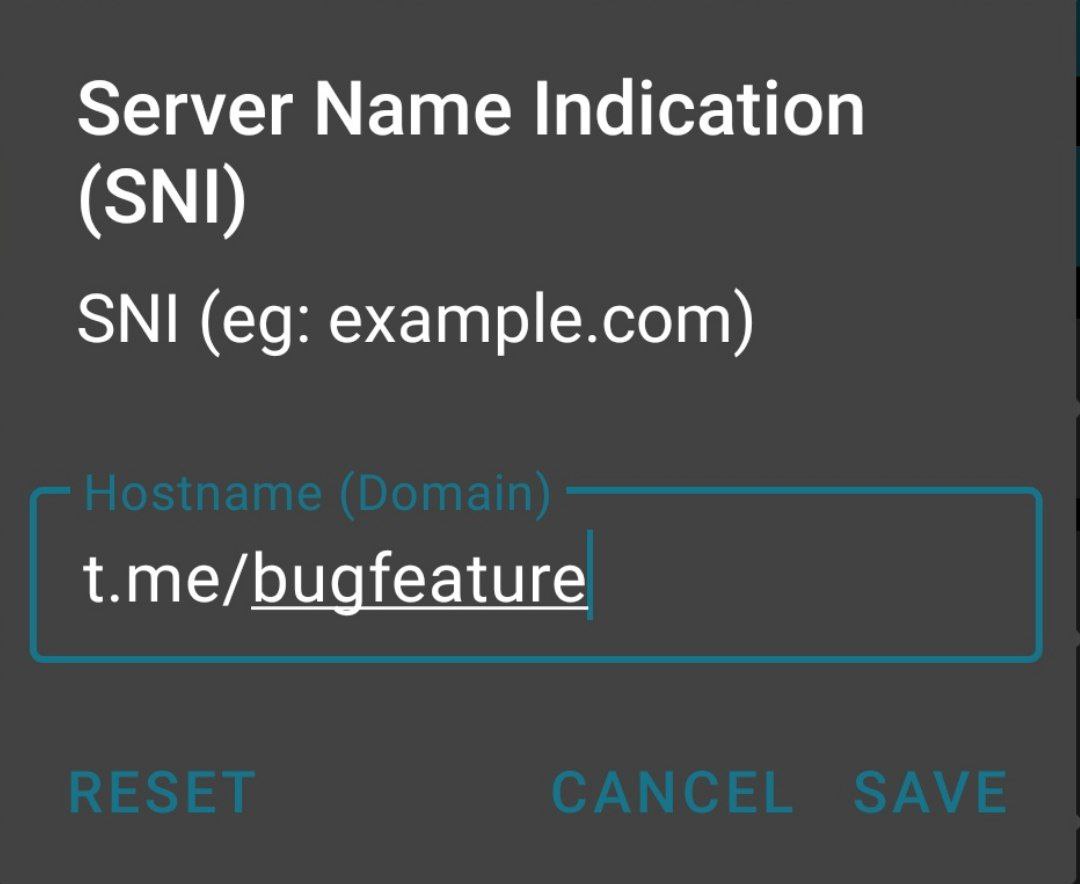
” href=”https://10alert.com/glossary/vpn/” target=”_blank”>In the SNI field, enter the site you want to disguise your traffic as.
3.
A VPN (Virtual Private Network) is used to provide staff are working remotely with secure access to the private network of a corporation or other organization, over the Internet. Encryption and other security features are used to maintain privacy and prevent unauthorized access to the private network.
” href=”https://10alert.com/glossary/vpn/” target=”_blank”>Select a server from the drop-down menu on the left.
4.
A VPN (Virtual Private Network) is used to provide staff are working remotely with secure access to the private network of a corporation or other organization, over the Internet. Encryption and other security features are used to maintain privacy and prevent unauthorized access to the private network.
” href=”https://10alert.com/glossary/vpn/” target=”_blank”>Press “Start”.
Ready.
A VPN (Virtual Private Network) is used to provide staff are working remotely with secure access to the private network of a corporation or other organization, over the Internet. Encryption and other security features are used to maintain privacy and prevent unauthorized access to the private network.
” href=”https://10alert.com/glossary/vpn/” target=”_blank”>Now the operator will see that you are visiting the specified site, and not your original traffic.
Note: If you wish, you can use your own
A network protocol for data transmission in encrypted form. SSH is used as a tunnel for other protocols (for example, TCP), which allows almost any content to be sent through it. SSH creates secure channels for password transfer, video streaming, and remote system control. An important feature of the protocol is data compression. A disadvantage
Read More
” href=”https://10alert.com/glossary/ssh/” target=”_blank”>SSH server.