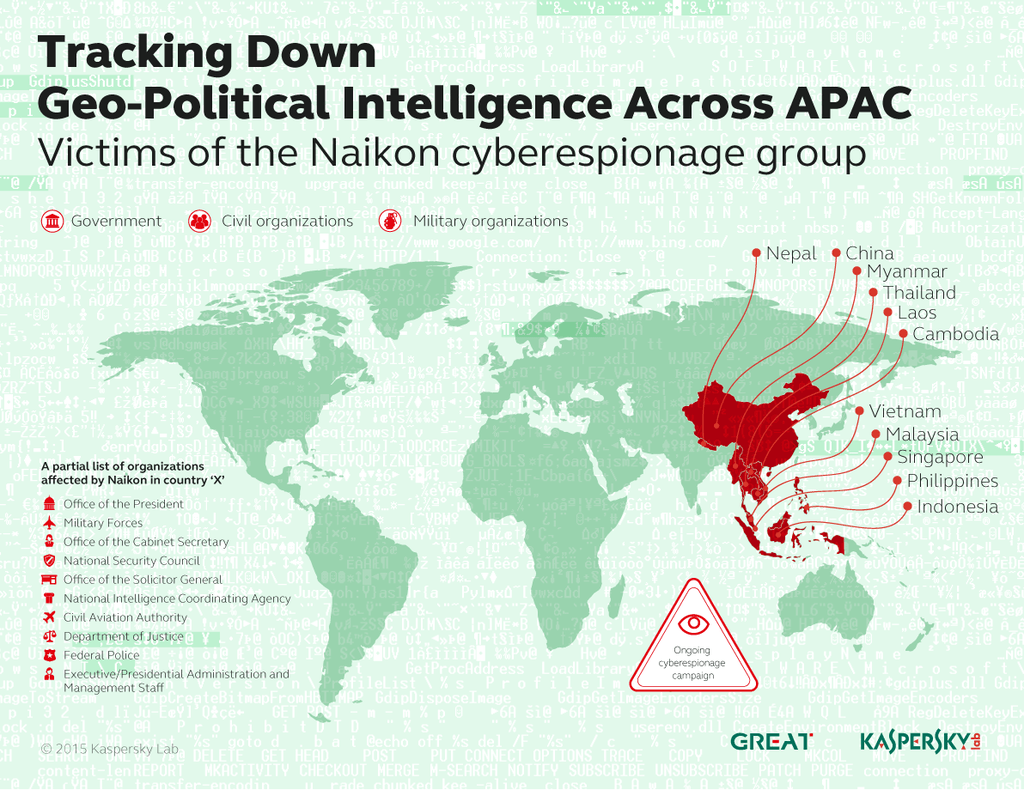
The Chinese-language Naikon advanced persistent threat group is targeting military, government and civil organizations located in and around the South China Sea, which is an increasingly contentious hot-bed of territorial disputes between various Southeast Asian nations.
Naikon is also known as APT-30. Its targets, according to a new report from Kaspersky Lab’s global research and analysis team, are said to include the Philippines, Malaysia, Cambodia, Indonesia, Vietnam, Myanmar, Singapore, and Nepal.
Like many APT campaigns, Naikon infects its victims with spear-phishing emails in which malicious executables masquerade as seemingly relevant document attachments. When a victim opens one of these malicious attachments, a decoy document appears as an executable file and quietly exploits an old Microsoft Office vulnerability, installing malware on the victim’s machine.
For five years, the APT group has employed cultural liasons for each of its target countries. In this way, Naikon is able to exploit cultural tendencies, such as the reliance on personal email addresses to conduct business. Attackers exploited this reality by creating email addresses that appeared similar to those in actual use, which the attackers were able to leverage to send more effective phishing messages.
Hellsing APT retaliates against Naikon attackers with own phishing ploy | http://t.co/fah3HZ81Aj pic.twitter.com/QUwv6hvzVK
— SCMagazine (@SCMagazine) April 15, 2015
The group has also installed portions of its command and control infrastructure in the target countries in order to provide daily support for real-time connections and data theft. They also have the capacity to intercept traffic across entire victim networks and issue some 48 distinct and remote commands, including taking a complete inventory of system files, downloading and uploading data, installing add-on modules, or working with the command line or prompt.
Taken together, these 48 commands allow the threat group to take complete control over any Naikon-infected machine. Naikon’s ultimate goal is to gather geopolitical information.
The criminals behind the Naikon attacks managed to devise a very flexible infrastructure that can be set up in any target country
“The criminals behind the Naikon attacks managed to devise a very flexible infrastructure that can be set up in any target country, with information tunneling from victim systems to the command center,” explained Kaspersky Lab principle security researcher, Kurt Baumgartner. “If the attackers then decide to hunt down another target in another country, they could simply set up a new connection. Having dedicated operators focused on their own particular set of targets also makes things easy for the Naikon espionage group.”
In one country that Kaspersky Lab declined to name, the Naikon hackers managed to compromise Office of the President, Military Forces, Office of the Cabinet Secretary, National Security Council, Office of the Solicitor General, National Intelligence Coordinating Agency, Civil Aviation Authority, Department of Justice, Federal Police and Executive/Presidential Administration and Management Staff.
The #Naikon #APT is designed to steal geopolitical information from nation’s located around the South China Sea
Tweet
Kaspersky Lab experts recommend that users never open attachments from people they don’t know, use an advanced anti-malware solution, and keep operating systems patched and up-to-date.
Source: kaspersky.com



