Unpatched Authenticated RCE in Oxygen and Breakdance Builder
Security Advisories
privilege escalation
rce
oxygen
breakdance
remote code execution
Published 4 April 2024 Updated 5 April 2024 Patchstack Table of Contents
Oxygen
Authenticated Remote Code Execution
Breakdance
Authenticated Remote Code Execution
This blog post is about an unpatched Remote Code Execution (RCE) vulnerability discovered in Oxygen and Breakdance builder. At the time of publication of this security advisory article, there is still no patch available on the latest version of the affected components. We hope that the developer will be implementing the proper security measures soon. In this article we will be explaining why this is important.
About the Oxygen and Breakdance Builder
The Oxygen and Breakdance builders (premium version) are two popular page builder plugins for WordPress. Both are owned & maintained by the same company – Soflyy.
The security vulnerability
These two builders are affected by an authenticated Remote Code Execution (RCE) vulnerability. This issue enables the lowest-permission user on both components to execute arbitrary PHP code. Despite both vendors insisting that this is an intended feature, permitting arbitrary code execution by the lowest-permission user on the component should not be allowed and goes against best security practices.
This vulnerability persists in the latest versions of Oxygen Builder (version 4.8.2) and Breakdance Builder (version 1.7.0). The aforementioned vulnerabilities are designated as CVE-2024-31380 and CVE-2024-31390.
Authenticated RCE in Oxygen
By default, Oxygen Builder restricts access to its features to users with the Administrator role. However, administrators have the option to grant permissions to specific roles on the WordPress site through the Client Control feature.
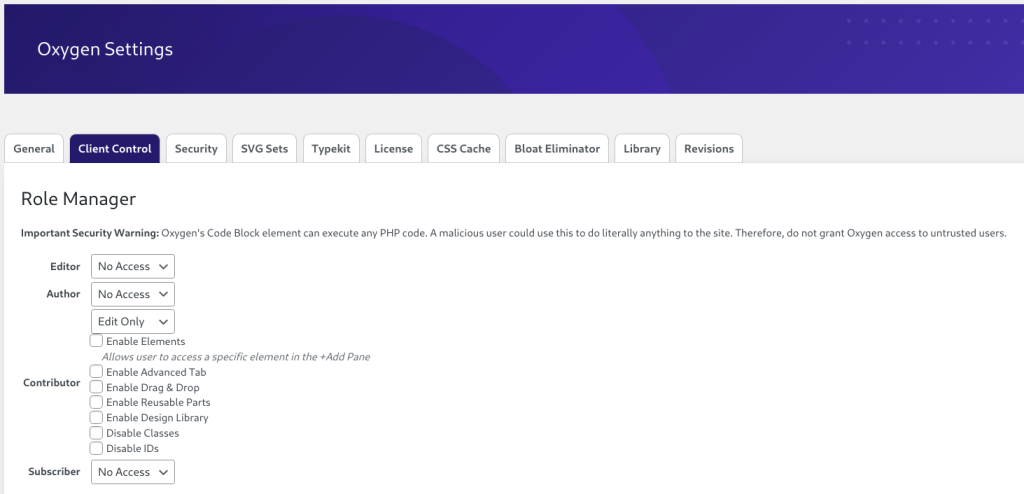
There is indeed a note regarding an Important Security Warning that essentially warns users that granting a user with Oxygen access could allow the user to execute arbitrary PHP code. Additionally, the vendor also has specific documentation regarding this feature that can be accessed here. Here is how the documentation looked like before we reported the vulnerability to them:
After receiving our report, the vendor originally admitted the vulnerability but requested a lower CVSS score. Later, they became determined that a patch was unnecessary, asserting that the issue was an intended feature and that warning the users about the security risk is enough.
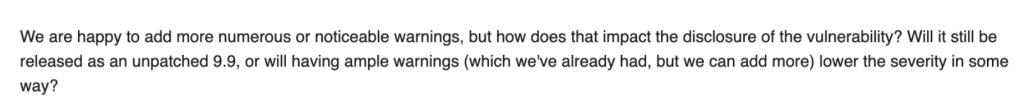
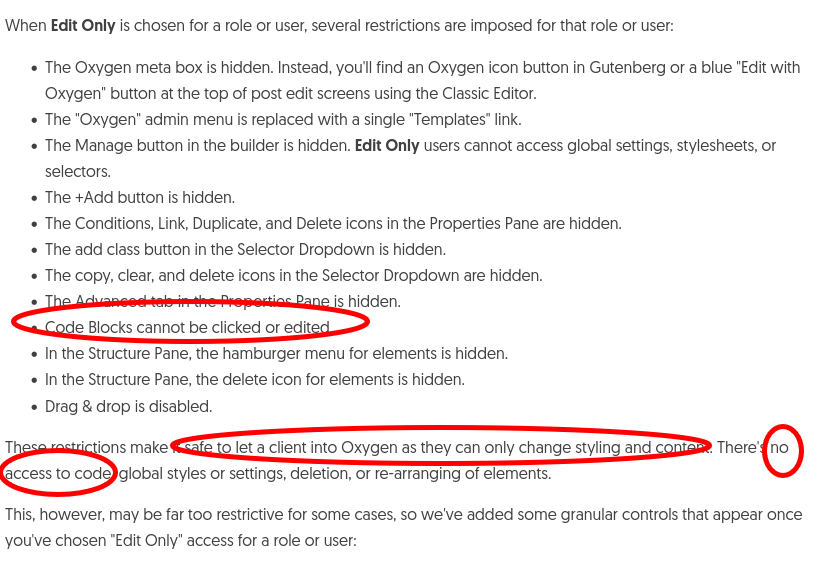
Subsequently, they updated the documentation as follows:
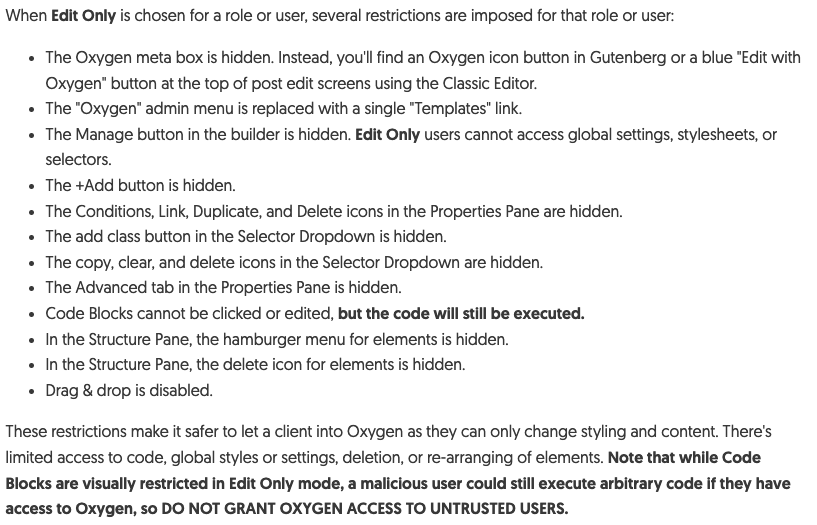
Notice on the previous version of the documentation, the Edit Only permission on the Client Control feature is supposed to be “safe to let a client into Oxygen as they can only change styling and content. There’s no access to code …” .
In many cases, administrators may grant limited access to the page builder of their WordPress site to agencies or contributors. The minimum realistic scenario typically involves providing ‘Edit Only‘ access to a Contributor role or higher, depending on the circumstances.
With this condition, a lower-permission user on the WordPress site can execute arbitrary PHP code, potentially leading to a complete takeover of the site and server. This deviates from the standard behavior of WordPress and contradicts the core principles of access control, wherein only users with an Administrator role or higher should be permitted to execute arbitrary PHP code.
On the technical side, let’s check how a user with Edit Only permission is able to execute arbitrary PHP code. One of the ways to achieve this is via the oxygen_vsb_current_user_can_access function:
close chevron-down chain bars angle-right angle-up cross menu
Source: patchstack.com



