Encrypting files in the browser so that no one can see them
Encryption of files is a reliable guarantee of their security. This is a very useful feature when you need to upload a file to the cloud or send it by mail. So you can be sure that an attacker will not be able to view your content.
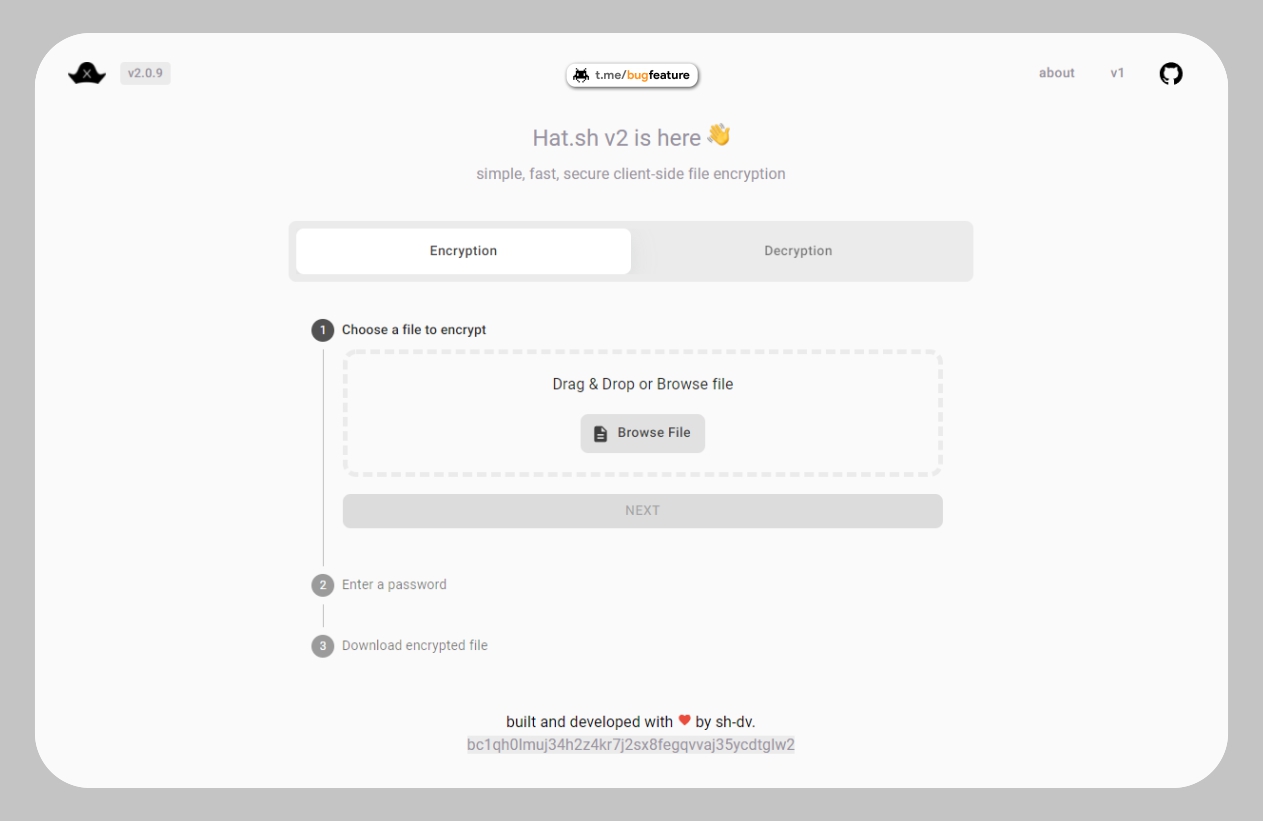
Hat.sh is a web application that provides instant secure encryption and decryption of files right in the browser. The service uses modern cryptographic algorithms with AEAD fragmented stream encryption/decryption.
Using it is very simple:
1. Select “ Encryption
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>Encryption
” to encrypt and “Decryption” for decryption. Encryption
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>
2.
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>Select the file to be encrypted.
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>
3.
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>Enter a password or generate an encryption key.
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>
four.
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>Download the encrypted or decrypted file.
The service is fast and secure.
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>The application runs locally in your browser and does not upload your files to a server.
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>No data is collected or sent to anyone.
Encryption describes the process of jumbling up data in such a way that it can not be easily understood by those who are not authorized to do so. The jumbled data is stored as ‘ciphertext’. A key, known as a decryption key, is required in order to access the original data. Encryption is used to Read More
” href=”https://10alert.com/glossary/encryption/” target=”_blank”>You can verify this by examining the source code available on GitHub
.