Wordfence Launches Bug Bounty Program to Fund WordPress Security Research and Showcase Researchers
At Defiant Inc and Wordfence, our mission is to Secure the Web. A critical component of creating and maintaining a secure online community is the research that reveals vulnerabilities in software. Without this research, only malicious hackers would find vulnerabilities, and they would quietly exploit the online community without any limit on the damage they can do.
Security researchers are the thin red line that stands between these hackers and their potential victims. Defiant Inc employs some of the most talented security researchers in the world, but we can not find all the vulnerabilities in the WordPress ecosystem on our own. We need help from the global army of talented and hard working researchers who dedicate their time to finding vulnerabilities in WordPress plugins and themes.
Today we are launching a Bug Bounty Program that provides security researchers with financial rewards for finding vulnerabilities, and for disclosing them privately to our program. These vulnerabilities will be triaged, confidentially disclosed to vendors who can implement a fix, that fix is released to secure the online community, and the vulnerability will ultimately be included in our public database once the software flaw has been fixed by the vendor, or after an appropriate amount of time has passed. This process is known in the industry as “responsible disclosure”.
We do not charge for our vulnerability database, including for API access, and for notifying developers of new vulnerabilities in real-time. But with this announcement, we are paying researchers for their hard work, thereby funding WordPress security research. This furthers our mission of securing the Web.
In the security community, we use the phrase “in-scope” to define the range of software and/or systems that are approved for cybersecurity research, like vulnerability analysis or penetration testing. Scope helps us focus on areas that are higher priority, and are approved for this kind of research. We use “scope” in our bug bounty program to clearly define where we would like researchers to focus their energy, and which areas of research will be most beneficial to WordPress site owners and site visitors.
There is no cap on the rewards an individual researcher can earn, and every single in-scope vulnerability received via our submissions process earns a reward bounty. Researchers can also create a public profile and unlock achievement badges, allowing them to highlight all of their contributions in one place. This draws attention to researchers who are making the biggest contribution to securing the WordPress community.
We believe we have improved the incentives that industry has historically provided with the way our bug bounty program works, and the focus of our program is exclusively on vulnerabilities related to WordPress. No more battling to reach the top of a leaderboard to earn rewards for your work, and no more hunting down Bug Bounty Programs that may or may not have WordPress plugins and themes as in-scope targets. We provide greater rewards for researcher contributions to the security of the WordPress ecosystem. With the Wordfence Intelligence Bug Bounty Program, researchers can focus their research on the areas that most effectively secure the online community, and be rewarded for their hard work.
As part of this release, we are having a launch party! For the first 6 months, all eligible vulnerabilities submitted will have a 10% bonus added to any bounties awarded. Get started now, or read more about the program first below!
Program Philosophy
Our Bug Bounty Program has been designed to have the greatest positive impact on the security of the WordPress ecosystem. Rewards are not earned by bulk hunting for vulnerabilities with minimal impact and earning a place on a leaderboard, but rather, they are based on active install counts, the criticality of the vulnerability, the ease of exploitation, and the prevalence of the vulnerability type.
The highest rewards are earned by unique, critical vulnerabilities, where there is an opportunity to patch the vulnerability before attackers discover and exploit it. Common vulnerabilities like authenticated Cross-Site Scripting and low-exploitability/low-impact vulnerabilities like Cross-Site Request Forgery earn the lowest rewards. This will direct research energy towards areas that most effectively secure the community.
Deeper Dive Into The New and Exciting Aspects of Wordfence Intelligence and the Bug Bounty Program
Researcher Profiles
One exciting feature we have introduced to Wordfence Intelligence, with the launch of the Bug Bounty Program, is the ability for researchers to register an account and create a public profile where they can add a small biography, link to select social media profiles, add a profile picture from Gravatar, and see their ranking on the researcher leaderboard. These profiles can be managed and edited at any point, though all profile updates will be moderated by our team. This page will also list any achievements granted to the researcher, which you can learn more about below, along with all vulnerabilities credited to the researcher.
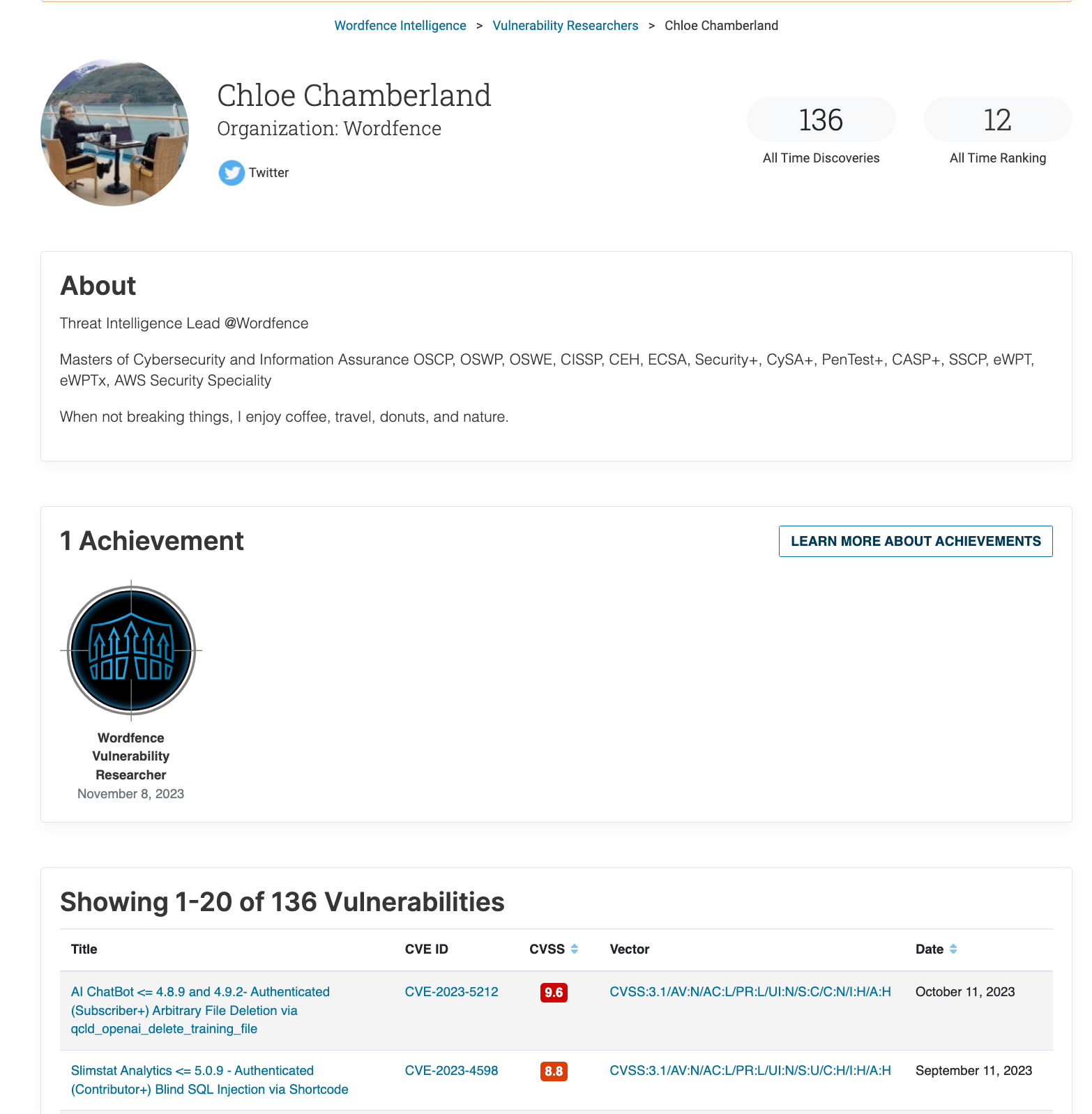
If you’re a researcher who already has vulnerabilities associated with a name in the Wordfence Intelligence database, you can register a profile and we will merge your existing vulnerabilities with your new account upon request, so that all of your historical vulnerabilities will show up on your profile. We recommend registering with your researcher name and/or alias that is present in the Wordfence Intelligence database for us to merge your data on initial profile approval, otherwise please send us an email at wfi-support@wordfence[.]com so that we can correctly merge your profile.
Register as a Researcher Now
Researcher Achievements
Another exciting feature we are introducing to Wordfence Intelligence with the launch of the Bug Bounty Program is researcher achievements! These are badges that researchers can earn when they have met specific criteria. Badges are a fun way to track progress and development, along with highlighting the accomplishments that security researchers make contributing to the WordPress ecosystem.
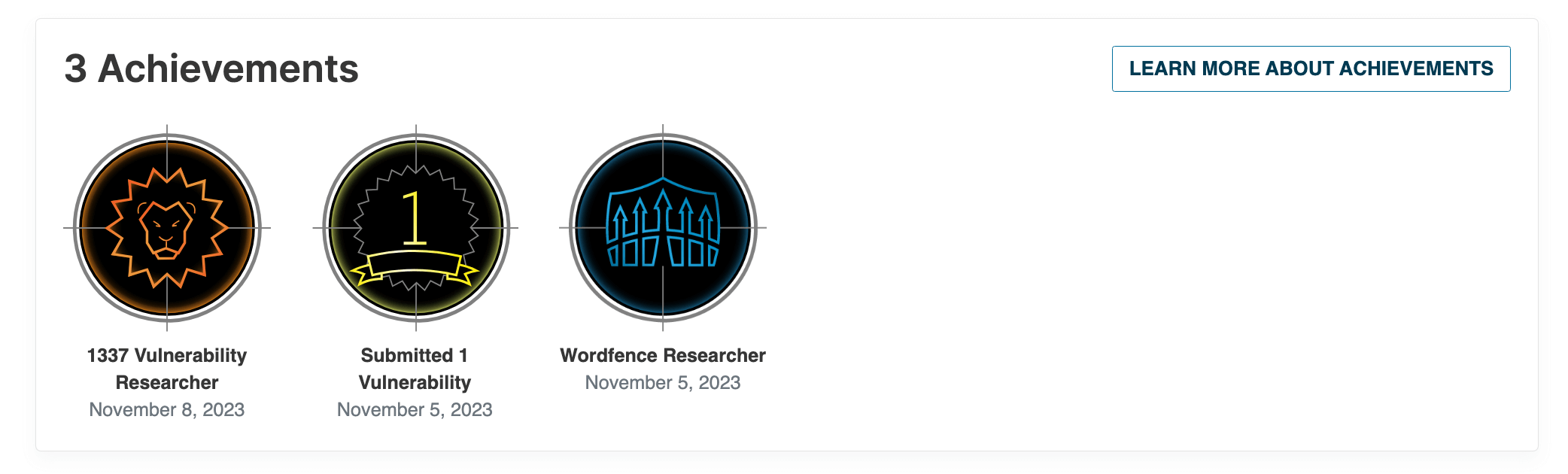
Everyone can easily earn at least one badge by submitting a valid vulnerability using our vulnerability submission form. The badge is granted once that vulnerability has been put into production.
Please note that the current researcher achievements available are not granted based on historical information, but are rather based on vulnerabilities submitted while authenticated as a researcher as part of our new vulnerability submission form. Vulnerabilities do not need to be eligible for a bounty in order for a researcher to be awarded a badge.
Learn more about Achievements
A New and Improved Way to Submit Vulnerabilities
With the launch of the Bug Bounty Program we needed to elevate our vulnerability submission process, so we are introducing the new Wordfence Vulnerability Submission Form, which has enhanced fields to make submitting quality vulnerability information easier. Researchers can choose from a variety of dropdown options for several of the fields. Even if you’ve used the CVE Request form in the past, we recommend you use this new form instead.
Users can utilize this form while unauthenticated to request a CVE or submit a vulnerability, however this will make them ineligible to earn any bounties. If this form is submitted while authenticated with a researcher account, the researcher will be eligible for a bounty as long as the vulnerability is in scope of the program.
We ask that researchers select ‘Yes’ to the question asking if the vulnerability being reported is out-of-scope when reporting an out-of-scope vulnerability so that it does not count towards your pending triage limit.
Submit A Vulnerability
Bug Bounty Program Bounty Rewards
Now for the most exciting part. Wordfence will now pay out bounty rewards for all in-scope vulnerabilities and software submitted to us through the vulnerability submission form, when all submitting rules and requirements have been followed.
All WordPress plugins and themes with over 50,000 active installations are in-scope for all researchers. This extends to plugins and themes with over 1,000 active installations for researchers with the “1337” Wordfence Vulnerability Researcher Status. In case you aren’t a security researcher, “1337” is shorthand for “elite” or “leet” in cybersecurity circles, and dates back to IRC hacker slang from the 1990’s.
We wanted to make it easy for researchers, so all vulnerabilities submitted through our new vulnerability submission form, while authenticated as a registered researcher, are eligible for earning bounties. By default, researchers can have 5 pending in-scope reports at any given time, while researchers with 1337 Wordfence Vulnerability Researcher Status can have 30 pending in-scope reports at any given time. Researchers can continue to submit vulnerabilities after the 5 pending limit, however, any additional vulnerabilities submitted after the limit are NOT eligible for bounties. A researcher must wait until their pending reports have been processed to submit more eligible reports, so we encourage researchers to submit the most critical vulnerabilities first and wait until those have been processed to submit more.
Bounties
Bounty rewards are dynamic, with the most impactful and critical vulnerabilities earning the most, and the least impactful and least likely to be exploited vulnerabilities earning the least. Here are some examples of the rewards you could earn:
- $1,600 for an Unauthenticated Arbitrary File Upload, a Remote Code Execution, a Privilege Escalation to Admin, or an Arbitrary Options Update in a plugin or theme with over one million active installations.
- $1,060 for an Unauthenticated Arbitrary File Deletion in a plugin or theme with over one million active installations, assuming wp-config.php can easily be deleted.
- $800 for an Unauthenticated SQL Injection in a plugin or theme with over one million active installations.
- $320 for an Unauthenticated Cross-Site Scripting vulnerability in a plugin or theme with over one million active installations.
- $80 for a Cross-Site Request Forgery vulnerability in a plugin or theme with over one million active installations, and a significant impact.
Please note that all reward rates are lower for lower active install counts. Reward rates are also lower for vulnerabilities that have privilege requirements to exploit.
Note: vulnerabilities that require high-level authentication (such as Editor and Administrator) to exploit are not eligible for bounties. Researchers who submit too many false positives, low quality reports, or out-of-scope reports may be banned or throttled from earning bounties in the program, so it’s important that researchers ensure they have thoroughly read the terms and conditions and put forth their best effort when reporting vulnerabilities to us.
Bonuses
All submissions will also be eligible for bonuses based on the research submitted to us. For the first 6 months, all bounties will be awarded a 10% additional bonus, automatically.
In the long term, researchers can also earn the following bonuses on any applicable vulnerability submissions:
- Chaining Master!
- A 15% bonus when a researcher is able to chain multiple vulnerabilities together in a single software product to achieve a critical impact.
- Creative Vulnerability Finder
- A 10% bonus when a researcher reports a vulnerability that hasn’t been seen before, or provides a clever way to bypass a mechanism, to achieve a critical impact.
- Meaningful Researcher
- A 10% bonus when the researcher thoroughly documents a vulnerability and makes it incredibly easy to reproduce the issue.
- 1337 Wordfence Vulnerability Researcher Program Bonus
- A 5% bonus for every vulnerability submitted once a researcher earns the 1337 Wordfence Vulnerability Researcher status.
- Affects Multiple Assets?
- A 10% bonus for every 10 software products affected by the same vulnerability, when the researcher thoroughly documents all software affected, up to a limit of 100 affected functions.
- Affects Multiple Functions?
- A 5% bonus for every 5 functions affected by the same vulnerability type, such as missing authorization, when the researcher thoroughly documents all functions affected, up to a limit of 50 affected functions.
- Handle Responsible Disclosure Yourself?
- A 5% bonus for any researcher who handles responsible disclosure themselves while following our responsible disclosure policy.
- Proof of Active Exploitation on an 0-day?
- A 15% bonus if a researcher reports a 0-day vulnerability that is being actively exploited prior to the vulnerability being disclosed or patched. This requires extensive evidence and corroboration on our side to prove any reported attacks are legitimate.
Learn More About Rewards
1337 Wordfence Vulnerability Researcher Program
The 1337 Wordfence Vulnerability Researcher program is designed to reward the very best researchers who have a proven track record for finding and reporting impactful vulnerabilities with high quality reports. Once a researcher earns this status, they will have a 1337 researcher badge added to their profile and will unlock the ability to earn bounties for plugins and themes within the 1,000 to 50,000 active install count range. They will also earn a 5% bonus on all bounty rewards, and can have 30 eligible reports pending at any given time. You can learn about how to earn this status by scrolling to the bottom of the page here.
Conclusion
Join our mission to secure the Web today by contributing your vulnerability research to The Wordfence Intelligence Bug Bounty Program, and get paid for helping to secure the online community.
You can sign up as a researcher here, or register at wordfence.com/account if you already have an account on wordfence.com. If you already have existing vulnerabilities within our database, we will be able to merge your newly registered account with all of your historical vulnerabilities so that you can showcase all of your work in one place. If you have already registered a profile and need these existing vulnerabilities assigned to it, please send an email to wfi-support@wordfence[.]com from the email that you registered with, and a link to the researcher page that needs to be merged with your account.
Source: wordfence.com



