Last year, we joined forces with Dutch law enforcement to launch the NoRansom website, which helps victims of CoinVault ransomware restore access to their data. Later, we enhanced the website with a couple of other free tools to restore files encrypted by other cryptors such as TeslaCrypt, CryptXXX, and others like them.
Today we’re taking another big step in our crusade against ransomware. Together with the Dutch police, Europol, and Intel Security, we created NoMoreRansom.org, a website where we plan to aggregate the widest selection of decryptors available anywhere.
We are starting by adding another virus cure to the website — one to help victims of Shade ransomware to restore their files. We offer it, like the others, free of charge.
Shade
Shade is a family of ransomware cryptors that emerged in early 2015. Shade Trojans use malicious spam or exploit kits as primary attack vectors. The latter is the more hazardous method because a victim does not have to open any files — a single visit to an infected website does the trick.
When the ransomware infiltrates a victim’s system, the Trojan requests an encryption key from the criminal’s command-and-control (C&C) server — or, should the server be unavailable, uses one of the keys embedded in advance. That means, even if the PC is disconnected from the Internet, the ransomware functions, provided it’s already in the system.
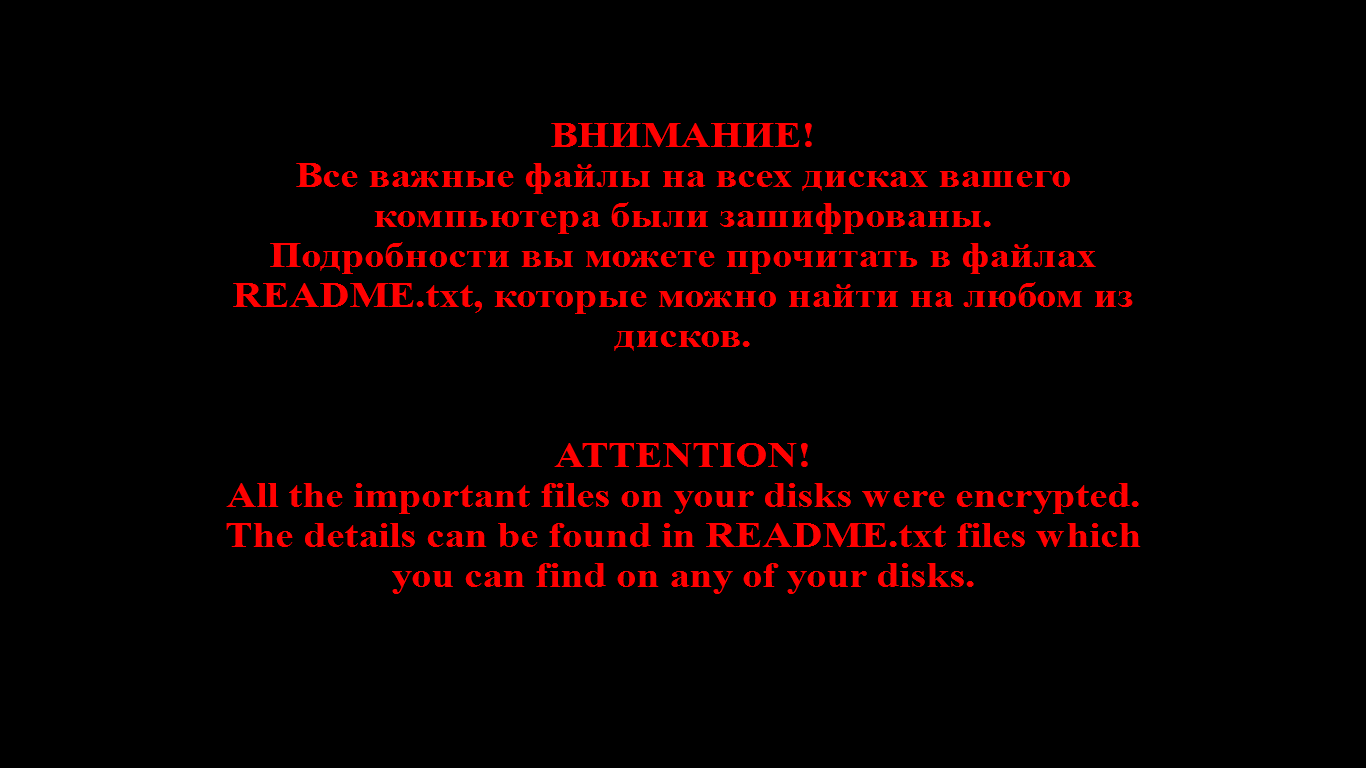
The malware then starts encrypting files. It affects more than 150 formats, including Microsoft Office files, images, and archives. When encrypting, Shade adds a .xtbl or .ytbl extension to the file name. Once the encryption process is complete, a ransom note appears on the screen.
As if the file encryption was not bad enough, the ransomware continues on its rampage: While the victim panics and searches for a decryptor — or money for ransom — Shade keeps busy, downloading other malware onto the compromised PC.
Get the free decryptor
If you were unlucky enough to fall victim to Shade, we have a spot of good news for you: We can spare you the temptation to pay ransom to get your encrypted files back. Here’s what to do:
1. Go to NoMoreRansom.org.
2. Scroll down and find the two download buttons for decryptors. You may choose the decryptor from Intel Security or Kaspersky Lab. The following instructions are for our own decryptor, however.
3. Unzip the downloaded file, ShadeDecryptor.zip.
4. Run ShadeDecryptor.exe.
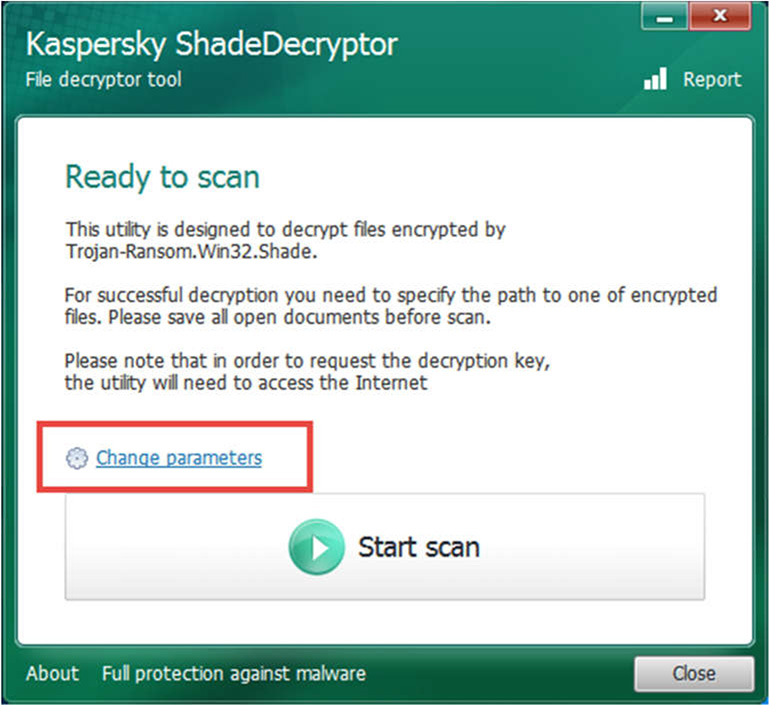
5. In the Kaspersky ShadeDecryptor window, click Change Parameters.
6. Choose which drives the utility should check for encrypted files.
7. In the same window, you may also choose “Delete crypted files after decryption,” but we do not recommend doing that until you are 100% sure your files have been restored.
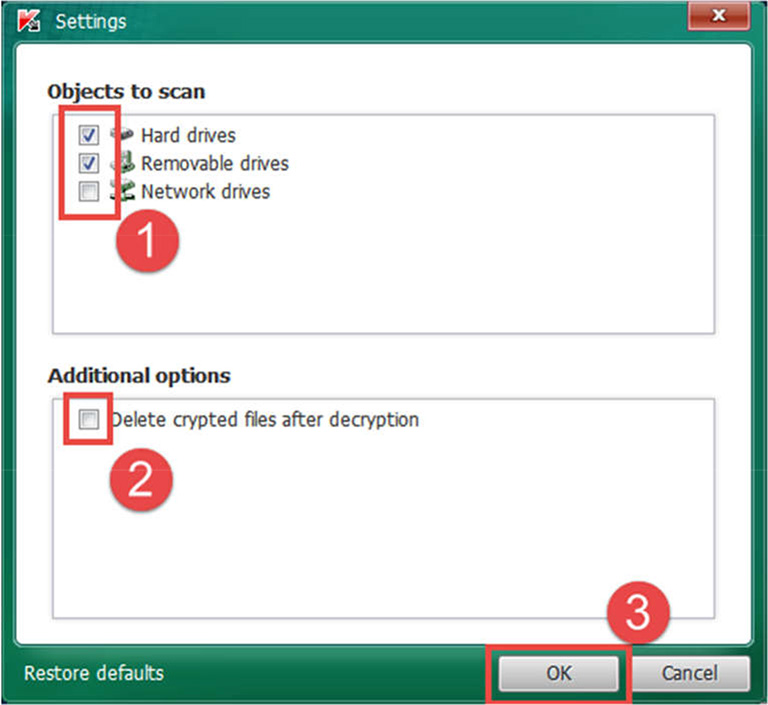
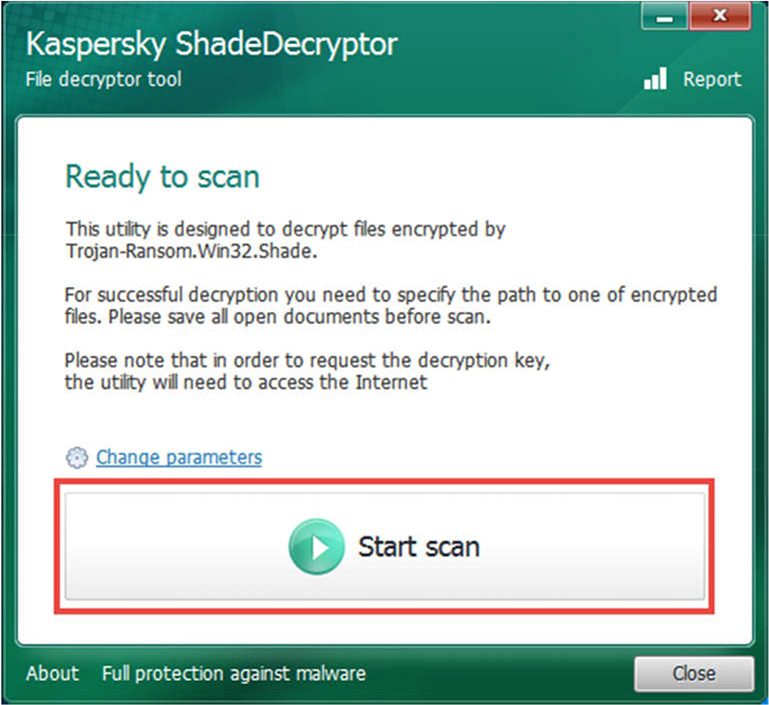
8. Click “ОК” to return to the main screen. Click Start scan.
9. In the “Specify the path to one of encrypted files” window, choose one of the encrypted files and click “Open.”
10. If the utility says it cannot automatically detect the victim’s ID, specify the file path to the readme.txt file, which is essentially the ransom note and which contains the ID in question.
Now your files should be decrypted. Enjoy the money you just saved! And to protect yourself from ransomware attacks in the future, use a robust security solution, such as Kaspersky Internet Security. For additional guidance on ransomware check out this post.
Source: kaspersky.com



