Researchers from Wordfence published a report about WP-VCD, one of the most serious threats to WordPress at the moment, which is responsible for infecting most sites running the popular CMS. Let me remind you that WP-VCD has been known since 2017, but since then the threat has become noticeably more serious. 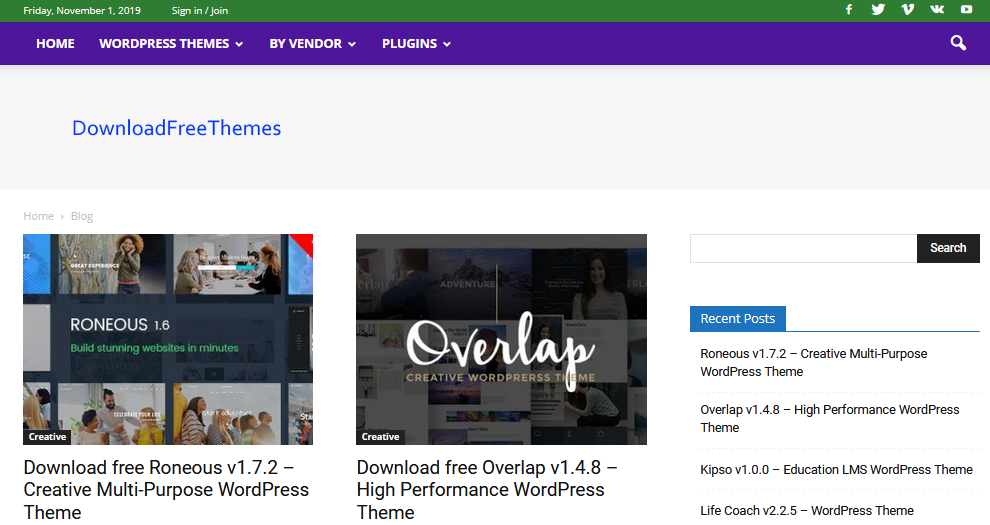
It is interesting that the attackers behind WP-VCD do not use vulnerabilities to penetrate other people’s sites and do not install backdoors. Instead, they rely on pirated (nulled) WordPress themes and plugins that people find and download on their own. The attackers operate a whole group of sites through which they distribute malicious themes and plugins, which are usually sold in private stores or on popular sites such as ThemeForest or CodeCanyon. The list of these sites includes: www.download-freethemes [.]download www.downloadfreethemes[.]co
www.downloadfreethemes[.]space www.downloadnulled[.]pw
www.downloadnulled[.]top www.freenulled [.]top www.nulledzip[.]download
www.themesfreedownload[.]net www.themesfreedownload[.]top
www.vestathemes[.]com
All of these resources have excellent SEO. They rank high in the search results, as all currently hacked sites infected with WP-VCD malware “help” them with keywords. As a result, a search on the name of any popular WordPress theme, combined with the word “download”, will result in two or three malicious sites appearing at the top of the Google search results. After users install malicious themes and plugins downloaded from these sites, WordPress is hacked, and control passes to the attackers after a few seconds.
So, first, the account 100010010 is added to the site, which plays the role of a backdoor and provides WP-VCD operators with access to the resource. WP-VCD is then added to all other themes on the site. This is done in case the user is only testing pirated themes and may soon get rid of them. And, finally, if the malware got on shared hosting, it tends to spread to the main server, infecting other sites hosted on the same system. Thus, users who protect their systems and do not use pirated products also suffer from WP-VCD, but they are not lucky enough to be “next door” to a less prudent administrator. As a result, the WP-VCD operators have at their disposal an impressive botnet of hacked sites that they have complete control over. According to Wordfence, the group is currently focused on two areas. The first is botnet development, which includes adding keywords and backlinks to infected sites. The second is the direct monetization of infected resources, which is carried out through advertising.
WP-VCD operators place ads on hacked sites, and these ads often contain additional malicious code that sometimes opens pop-up windows or redirects users to other malicious resources. For this, the group receives money from other criminals.
According to information Wordfence, some WP-VCD operator domains were registered by a person named Sharif Mamdouh. In addition, some of these domains have also been linked to attacks on Joomla sites back in 2013. However, it is not yet clear whether this person is one of the attackers, or whether his identity was simply stolen.





