Start FREE
🎉 NEW: Community IP Blocklist – automatically block IPs known to exploit vulnerabilities!
WordPress 6.4.3 Security Release
Security Advisories
wordpress
Published 31 January 2024 Rafie Muhammad Security Researcher at Patchstack Table of Contents
WordPress 6.4.3 was released on January 30th, 2024, which includes two low-severity security fixes.
This security fix addresses two potential security issues. The first one is an Administrator+ arbitrary PHP file upload on the plugin and theme upload functionality. The second issue is a potential security issue that can only be exploited if another vulnerability (PHP object injection) is already present on your WordPress site.
We highly recommend you update your site to version 6.4.3 (or one of the patched versions) as soon as possible. Sites with plugins or themes installed that contain a PHP object injection vulnerability are especially at risk, so it should be a high priority to update WordPress on your site.
Patches for the two issues have been backported to version 4.1 and later on the WordPress Core.
Technical analysis
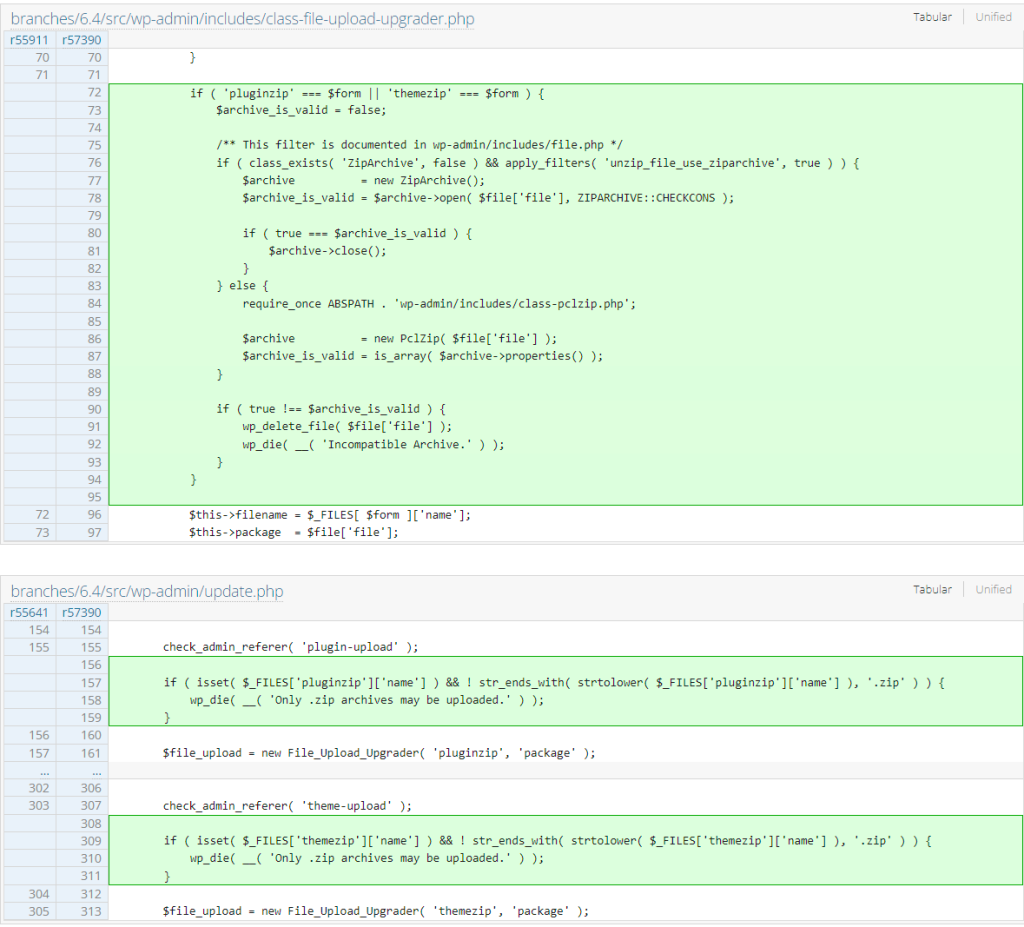
Administrator+ Arbitrary PHP File Upload
WordPress Core
Administrator+ Arbitrary PHP File Upload
This security issue has existed since 2018. This allows the Administrator user role and Super Admin user role on multisite environments to upload PHP files directly to the site through the plugin and theme upload functionality. Note that this is only an issue if the site is implementing a process to limit the Administrator and Super Admin user role to upload a plugin or theme. The patch for this issue can be seen below:
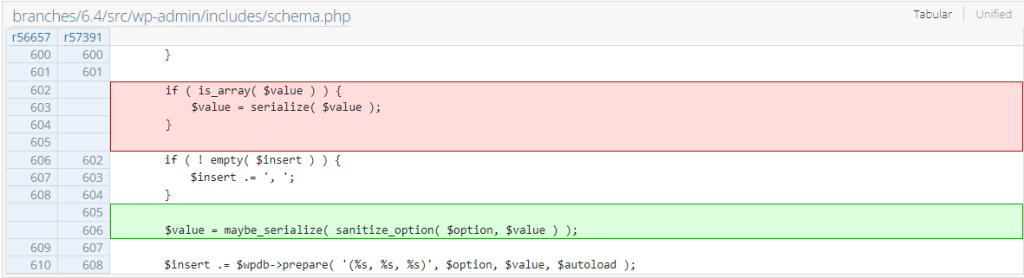
Potential PHP Object Injection Gadget
This potential security issue will not make it into our vulnerability database as this can become exploitable only if a PHP object injection exists somewhere on the targeted WordPress site.
According to the release article, the Core team patched a potential PHP object injection gadget that could be used to gain Remote Code Execution (RCE) on the WordPress site. We notice that there is a change in how the options are stored. The process now involves sanitization using the sanitize_option function before applying another serialization process using the maybe_unserialize function. The option sanitization apparently doesn’t get implemented during site installation and upgrade process in older versions. The patch can be seen below:
Since the two issues require a very high permission role or an incomplete site installation or upgrade process, there is only a very small chance that these issues will be exploited in a real-world case.
Found this useful? Share on
Detect vulnerabilities and protect your WordPress apps. See features
The latest in Security Advisories
AI Engine Plugin Affected by Critical Vulnerability
Critical Vulnerability
arbitrary file upload
AI Engine
 20 December, 2023
20 December, 2023
Critical SQL Injection Found in Porto Theme’s Plugin
Premium Theme
Critical Vulnerability
SQL Injection
Porto
 12 December, 2023
12 December, 2023
Multiple Vulnerabilities Patched in Themify Ultra Theme
arbitrary file upload
php object injection
theme
themify
settings change
Protection
Pricing WordPress For agencies Documentation
Solutions
WordPress security Plugin auditing Managed VDP Bug bounty Intelligence (API)
Bug bounty
Leaderboard Security programs Guidelines Report
Resources
Vulnerability database Whitepaper 2022 Articles Join Discord
Patchstack
Careers Media kit LinkedIn Facebook X  © 2024 Patchstack DPA Privacy Policy Terms & Conditions
© 2024 Patchstack DPA Privacy Policy Terms & Conditions 
Protection
Pricing WordPress For agencies Documentation
Solutions
WordPress security Plugin auditing Managed VDP Bug bounty Intelligence (API)
Bug bounty
Leaderboard Security programs Guidelines Report
Resources
Vulnerability database Whitepaper 2022 Articles Join Discord
Patchstack
Careers Media kit LinkedIn Facebook X © 2024 Patchstack DPA Privacy Policy Terms & Conditions
This website uses cookies. Learn more.
Looks like your browser is blocking our support chat widget. Turn off adblockers and reload the page. Reload page
close chevron-right chevron-down chain bars angle-right angle-up cross menu
Source: patchstack.com