Fake Tor Browser Stealing Darknet Users’ Darknet
A darknet is an overlay network (i.e. a network built on top of another network – in this case, the Internet) that isn’t discoverable by normal methods and can only be accessed using special software like Tor. Darknets are designed to preserve the privacy of those using them. Traffic is routed through a network of
” href=”https://10alert.com/glossary/darknet/” target=”_blank”>Cryptocurrency
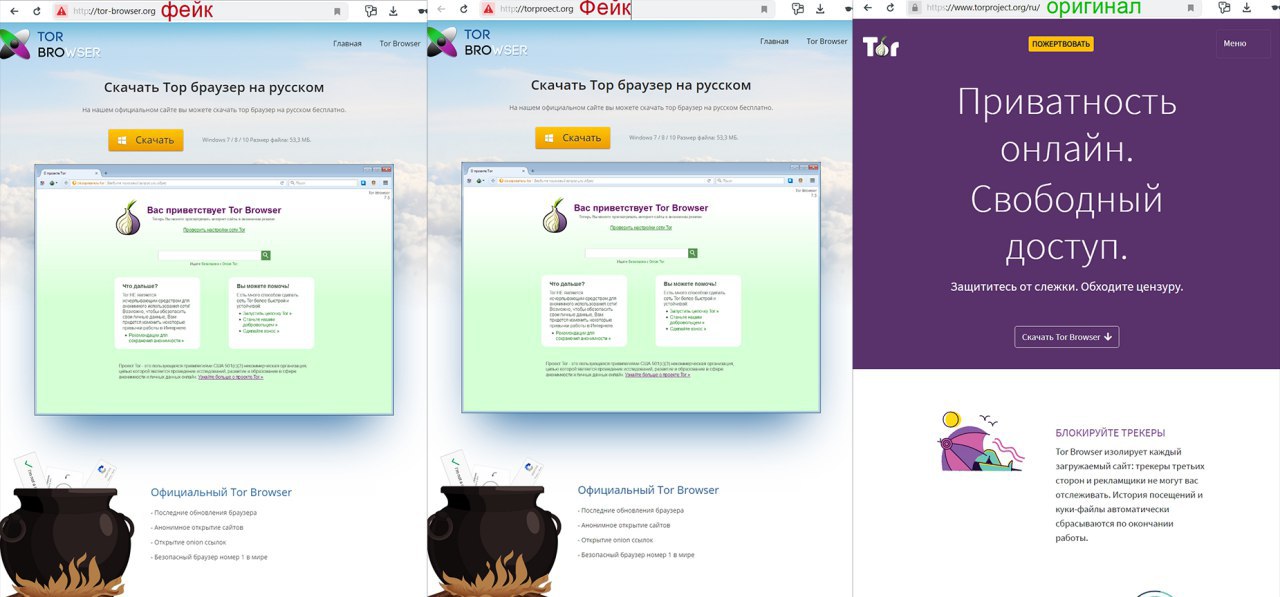
The attack is aimed at Russian-speaking users, and is presented in the form of two fake Tor sites that were created back in 2014:
One of the protocols used to transmit data on the Internet. Originally developed as a standard for sending HTML documents, it is currently used to transfer various types of data. Each HTTP packet consists of a starting line, header, and message body. The core technology is the interaction between data supplier and consumer. The client
Read More
" href="https://10alert.com/glossary/http/" target="_blank">http://tor-browser.org/
http://torproect.org/The sites were promoted in 2017 and 2018 on the resources darknet themes. HTTP
One of the protocols used to transmit data on the Internet. Originally developed as a standard for sending HTML documents, it is currently used to transfer various types of data. Each HTTP packet consists of a starting line, header, and message body. The core technology is the interaction between data supplier and consumer. The client
Read More" href="https://10alert.com/glossary/http/" target="_blank">For example: drugs, cryptocurrency, censorship circumvention and politics.Visitors were asked to install a fake browser under the pretext of bypassing blocking, CAPTCHA, tracking and supporting the Russian interface language.
At the same time, a hard-coded value
HTTPUser-Agentin the browser.One of the protocols used to transmit data on the Internet. Originally developed as a standard for sending HTML documents, it is currently used to transfer various types of data. Each HTTP packet consists of a starting line, header, and message body. The core technology is the interaction between data supplier and consumer. The client
Read More" href="https://10alert.com/glossary/http/" target="_blank">Thus, it can be used for surveillance as a user fingerprint:Mozilla/5.0 (Windows NT 6.1; rv:77777.0) Gecko/20100101 Firefox/52.0The basic task of a fake browser is to replace the copied Qiwi number and bitcoin address during transactions by the user.
During the existence of these sites, the Bitcoin
Bitcoin is a digital cryptocurrency that emerged in 2008 as the brain-child of 'Satoshi Nakamoto' and was released as open-source software in 2009. Trading occurs on a peer-to-peer basis and is not regulated by a central authority. Instead of having a printed bill or minted coin, Bitcoin values are represented as a cryptographic string of
Read More
" href="https://10alert.com/glossary/bitcoin/" target="_blank">bitcoin-wallets of scammers received approximately $40 thousand. There is no information about the balance of the Qiwi-wallet.