Despite some instability over the past six months, the cryptocurrency market is still seen by many as a get-rich-quick scheme. Accordingly, the stream of scammers feeding off this topic won’t be running dry any time soon. To lure victims into their traps, they continue to come up with new ploys, each more innovative than the last. Today we look at a novel scheme that invites victims to withdraw funds supposedly mined by their accounts on some kind of “automated cloud-mining platform.”
While you were gone, your account got mined
It all starts with an e-mail with an attached PDF informing the recipient that nearly a year has passed since they last logged in to their “Bitcoin Cloud Mining” account, which they supposedly created once upon a time. In the interim, the scammers write, 0.7495 BTC (worth around US$15,000) has accumulated in the account. But here’s the rub: since the account has been dormant for almost a year, it will be blocked very soon — after which the mined cryptocurrency will be distributed among other platform users. Time is of the essence, though it’s not clear precisely how much of it the user actually has: the e-mail states “2 days 23:58:38” in a large font, while the small print reads “within 24 hours”. Either way, not everything is lost: the user still has time to log in and withdraw the funds.
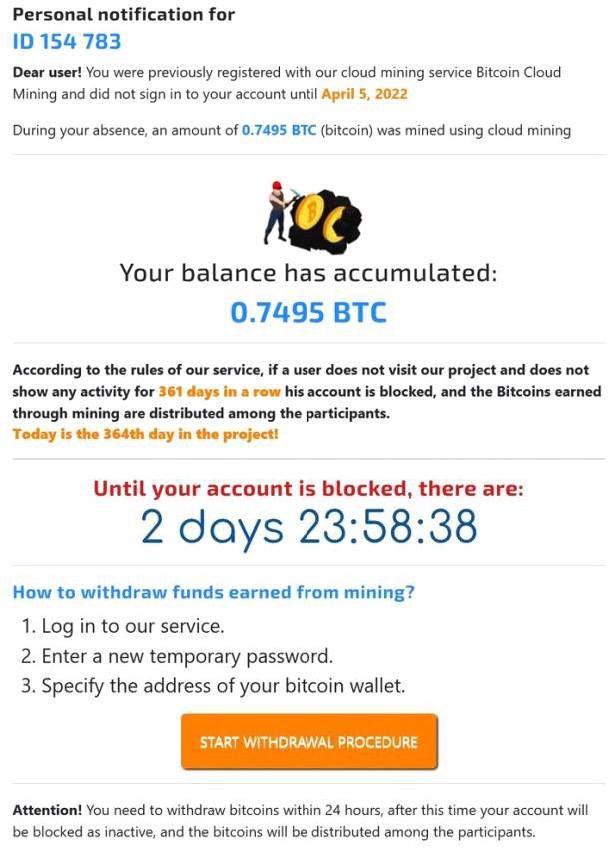
In the attached PDF, scammers promise a large payout if the victim logs in right away; otherwise the account will be blocked
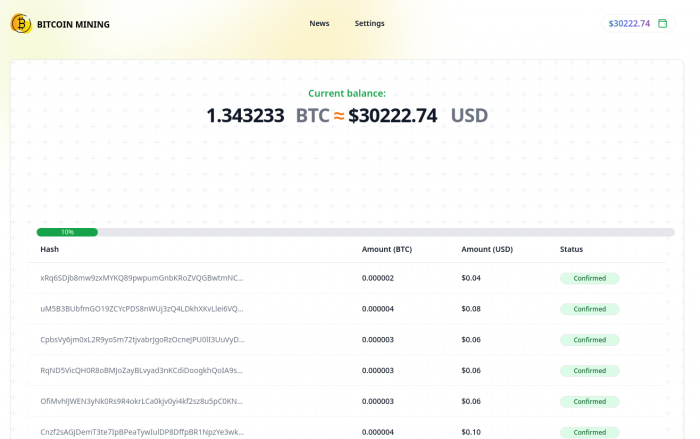
After clicking the button in the file, the user is taken to the mentioned “Bitcoin Mining” website (the word “Cloud” has been dropped out of the name by this point). There, two pieces of good news await. First, it turns out that the platform remembers the user by their IP address, so there’s no need to recall the username and password. Second, the payout has now gone up to 1.3426 BTC – a little more than US$30,000 at the time of posting.
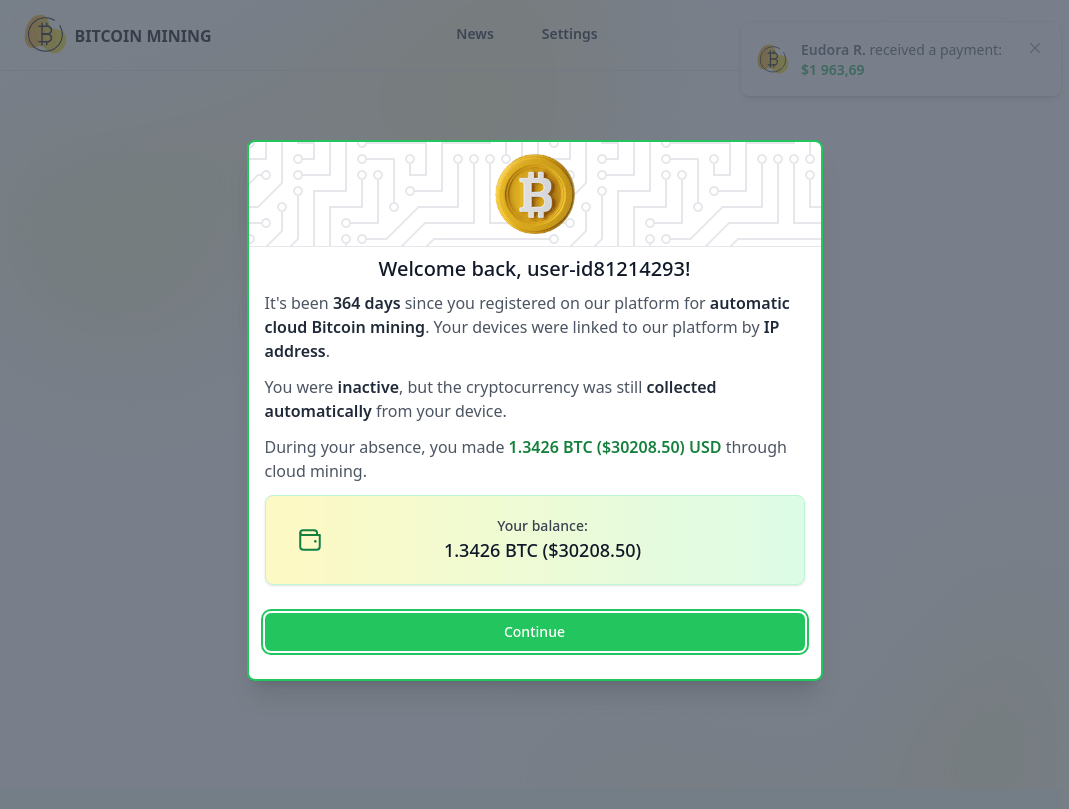
Fake Bitcoin mining platform claims to remember the user’s IP address
Now for the bad news: even less time now remains than was specified in the e-mail. The account will be blocked in precisely 18 hours, 39 minutes, 54 seconds — so get those skates on!
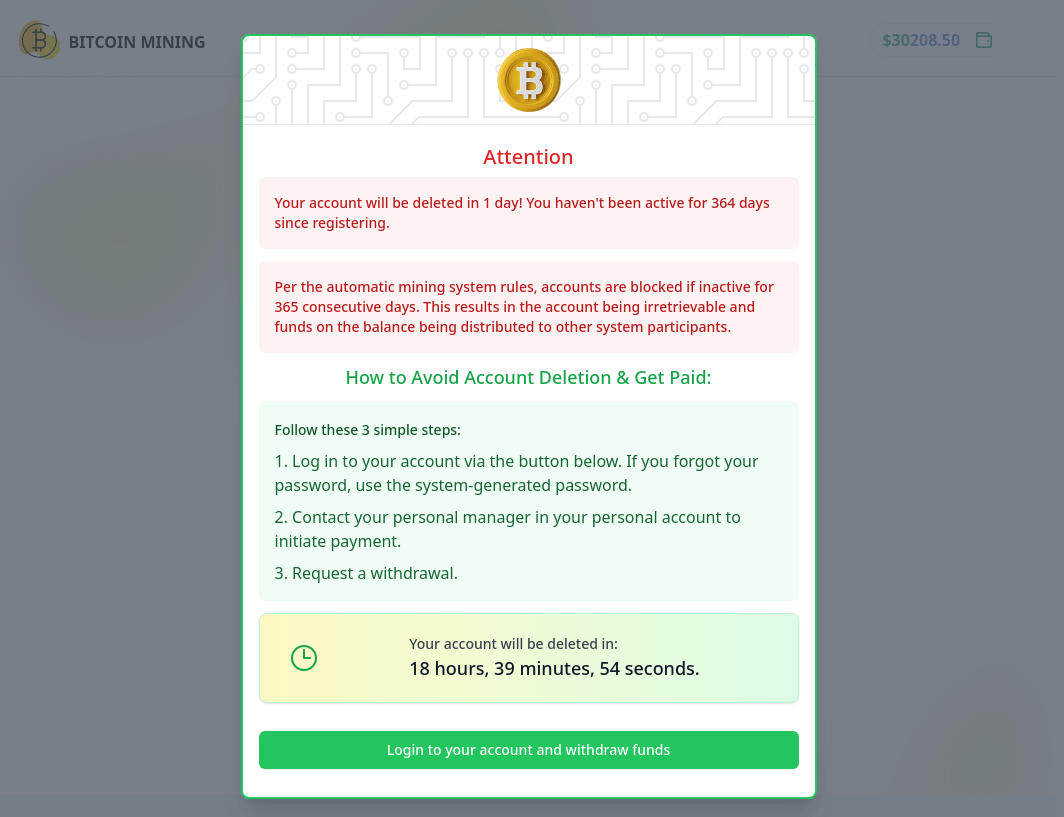
Scammers rush the victim: no time to lose!
The username and password are already auto-filled in the form; all that remains is to click the login button.
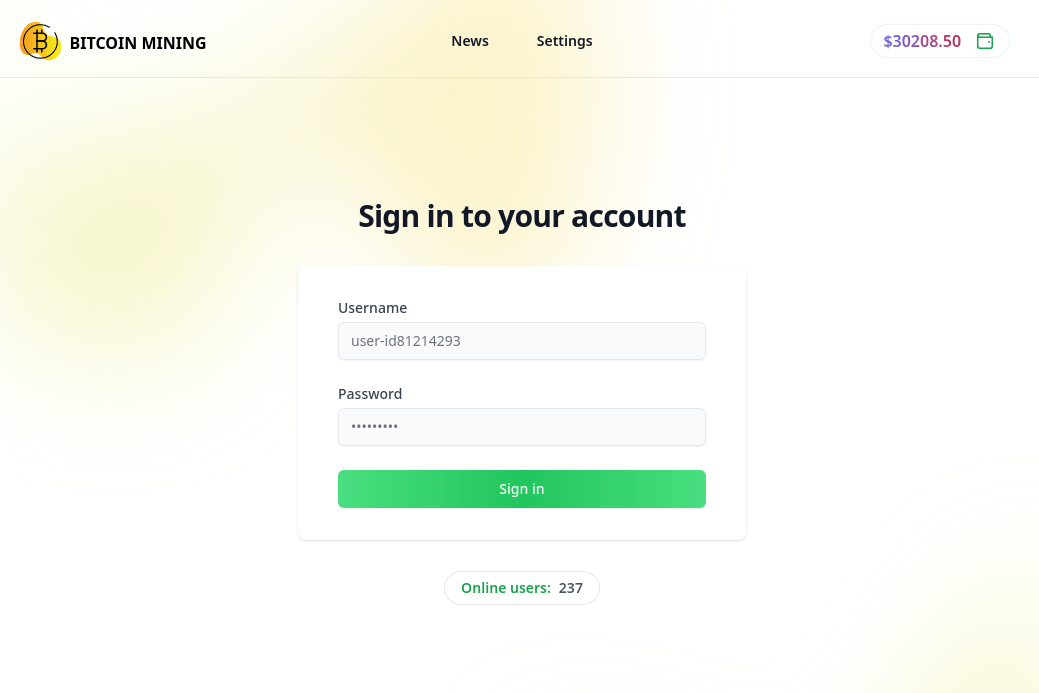
There’s no need to remember the username and password, they are auto-filled
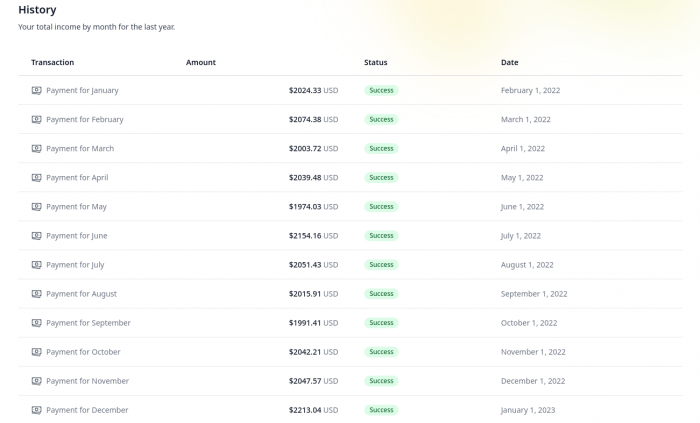
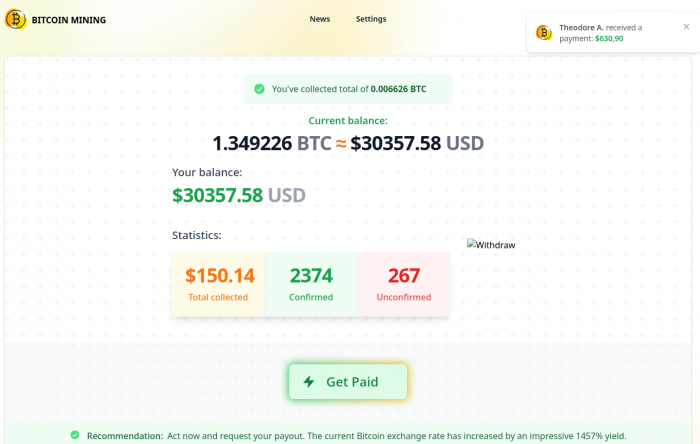
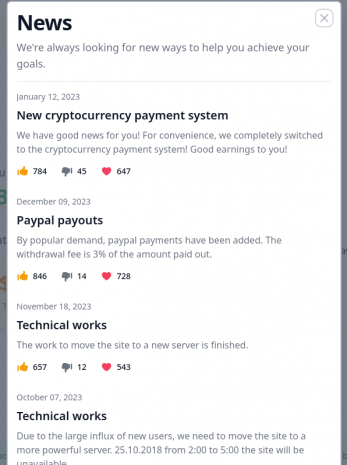
The fake site is surprisingly detailed, with lots of different sections to explore. For example, there’s a monthly history of accruals, a history of rewards for individual mining operations, a colorful page showing the current balance, and even a news section. Besides, occasional notifications pop up in a corner of the window stating that some other user just got a large payout.
- The scam site is surprisingly well designed
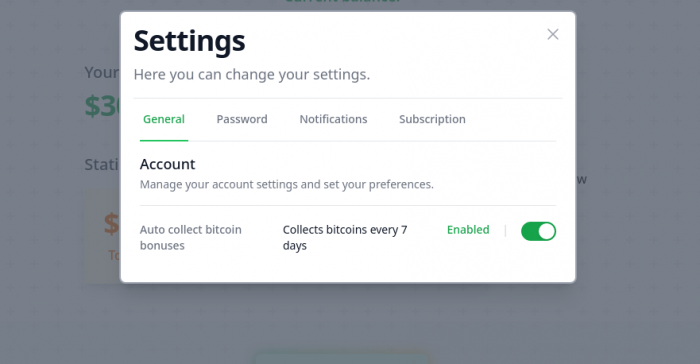
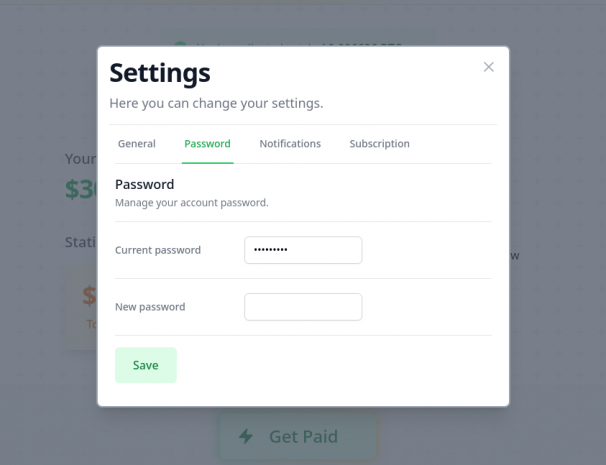
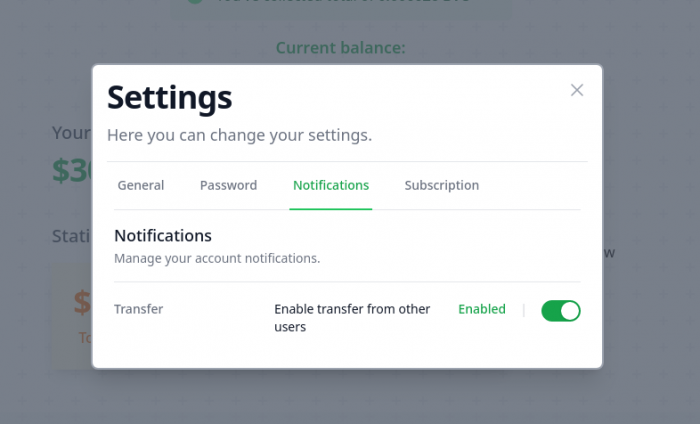
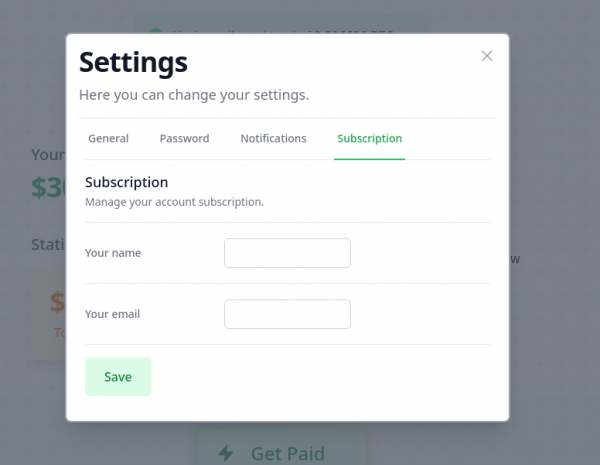
There’s a “settings section” for changing the password, subscribing to various services, enabling auto-withdrawal of funds (not specified where to), and even allowing other users of the platform to send you money (on the notification settings tab, for some reason).
- The scam site even has a settings section
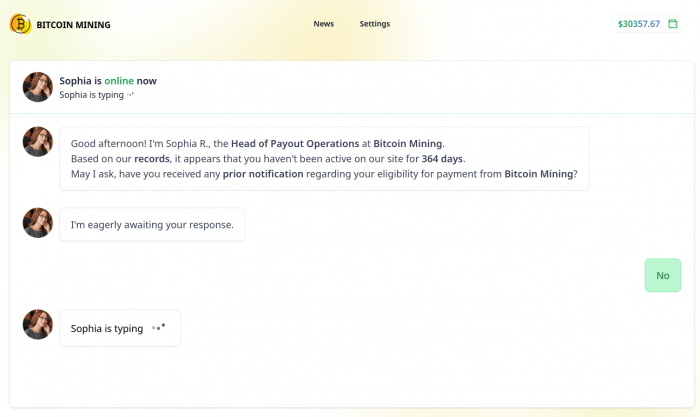
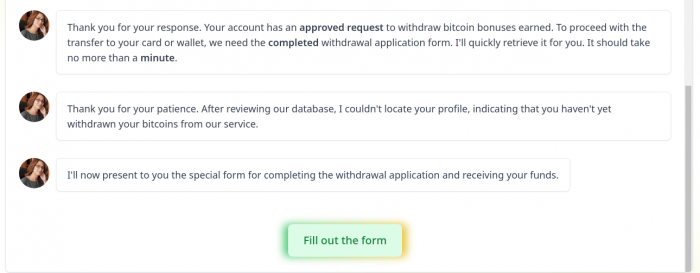
The focal point for the victim, of course, is the “Get payout” button. Clicking this button initiates what seems to be a chat between the user and a certain Sophia, who appears to be the Head of Payout Operations. Another form has to be filled out, this time with personal data, including card number (presumably the site creators collect this information to sell on).
- During the chat with the “Head of Payout Operations”, the user is asked to enter their personal data, including card number
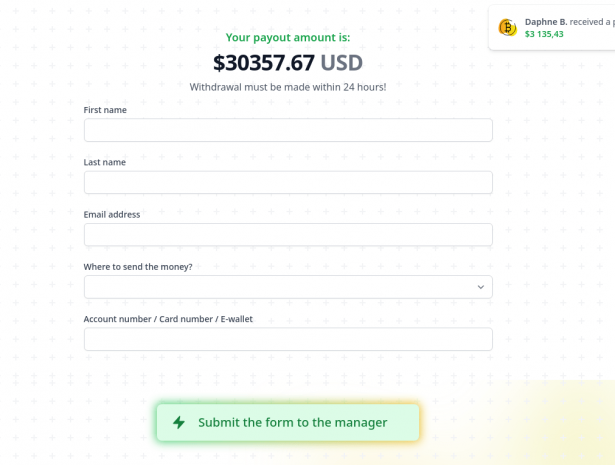
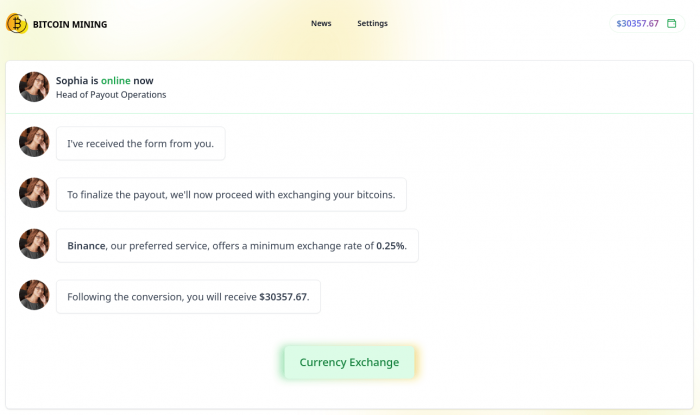
Of course, the scammers’ goal is to squeeze real money out of the victim. So pretty soon they get down to brass tacks. The victim is offered to convert the cryptocurrency into dollars by paying a small commission of 0.25%. In monetary terms, the fee turns out to be even less than that — just $64.03.
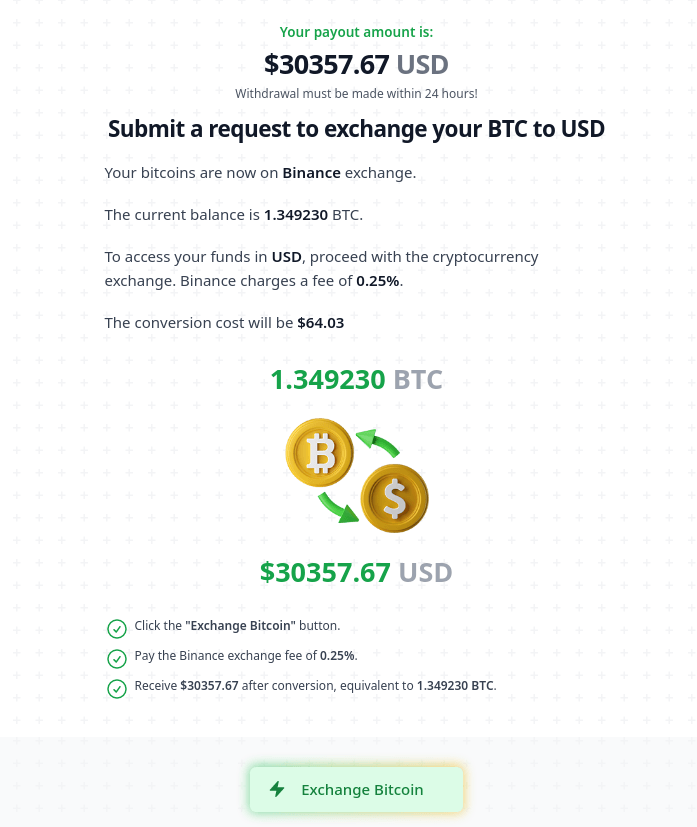
A small commission is charged to convert bitcoin into regular money
The “fee” must be paid in cryptocurrency, so the user is transferred to a page explaining how to purchase it.
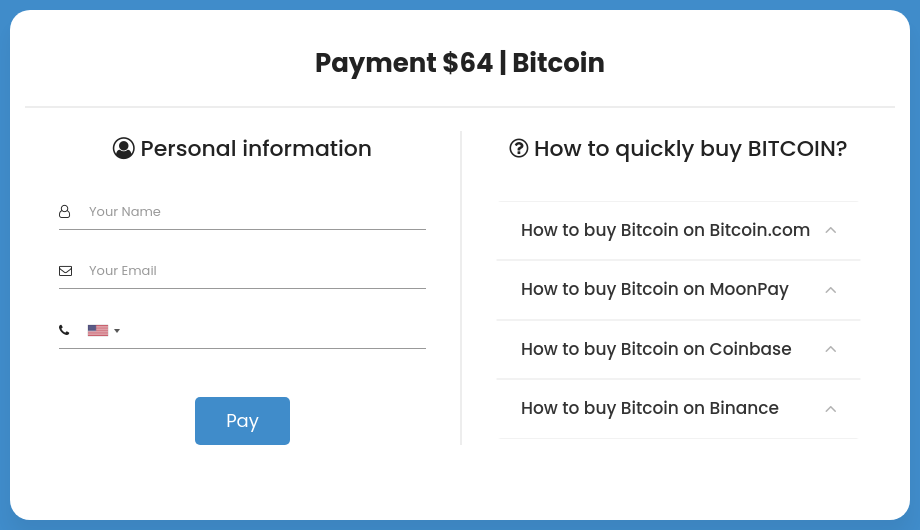
Customer care: the scam site kindly explains how to buy bitcoin
After clicking the “Pay” button, a page appears with the wallet address for sending the “fee”.
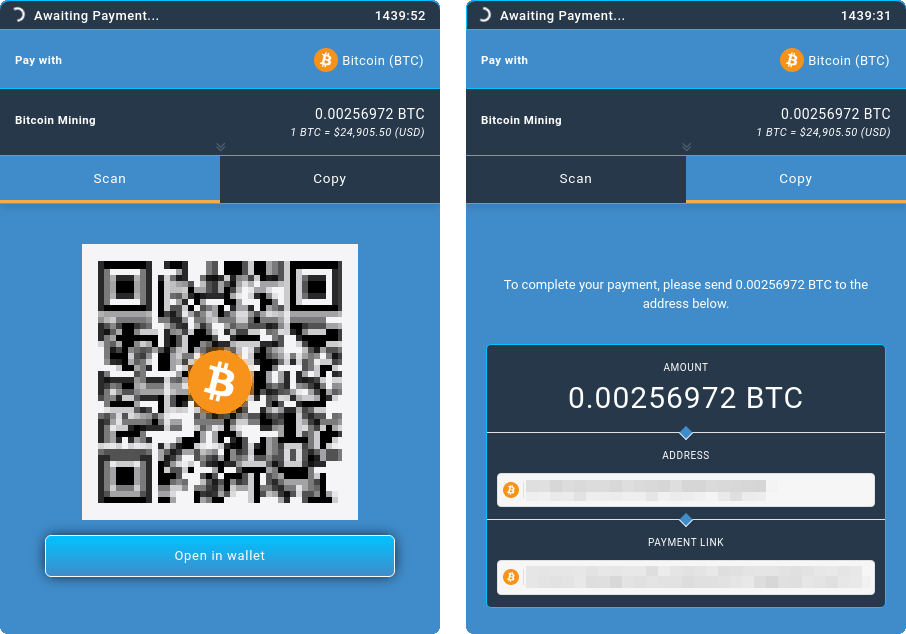
Send the payment here
Sure, after paying the “fee”, the victim receives not a penny of the promised payout, but has handed their payment and personal information to the attackers, who can then use it in other schemes or sell it on the dark web.
How to stay safe
Now for a few tips on how to protect yourself from this and other scams:
- Don’t be fooled by sudden generous gifts: large no-strings-attached payouts. If someone dangles large winnings in front of your nose, it will probably end in tears.
- Learn to recognize online scams. There are several telltale signs, which we covered earlier.
- Never enter card details on suspicious sites.
- Don’t send cryptocurrency to strangers — you won’t be able to appeal the transaction and get your money back.
- Install a reliable security solution with built-in protection against phishing and online fraud. This will warn you in advance if you’re about to land on a dangerous site.
Source: kaspersky.com