WebToffee Addresses Authentication Bypass Vulnerability in Stripe Payment Plugin for WooCommerce WordPress Plugin
On June 8, 2023, our Wordfence Threat Intelligence team identified and began the responsible disclosure process for an Authentication Bypass vulnerability in WebToffee’s Stripe Payment Plugin for WooCommerce plugin, which is actively installed on more than 10,000 WordPress websites. This vulnerability makes it possible for an attacker to gain access to the accounts of users who have orders. These users are typically customers but can include other high-level users when the right conditions are met.
Wordfence Premium, Wordfence Care, and Wordfence Response users received a firewall rule to protect against any exploits targeting this vulnerability on June 19, 2023. Sites still using the free version of Wordfence will receive the same protection on July 19, 2023.
We contacted WebToffee on June 8, 2023, and received a response the next day. After providing full disclosure details, the developer released a patch on June 13, 2023. We would like to commend the WebToffee development team for their prompt response and timely patch.
We urge users to update their sites with the latest patched version of Stripe Payment Plugin for WooCommerce, version 3.7.8 at the time of this writing, as soon as possible.
Vulnerability Summary from Wordfence Intelligence
Description: Stripe Payment Plugin for WooCommerce user_id : $order->get_user_id();
wc_set_customer_auth_cookie( $userID );
}
wc_add_notice( __( ‘You have cancelled Stripe Checkout Session. Please try to process your order again.’, ‘payment-gateway-stripe-and-woocommerce-integration’ ), ‘notice’ );
wp_redirect( wc_get_checkout_url() );
exit;
}
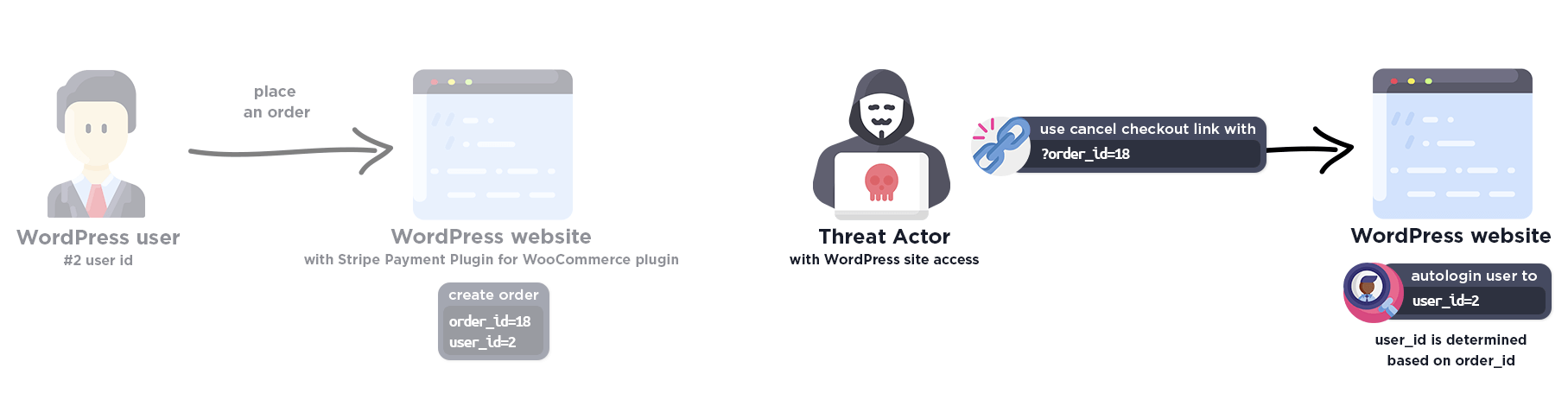
If the link contains the ‘createaccount‘ parameter and its value is ‘true‘, the plugin will log the customer in based on the order id, without any authentication. This means that it is possible to create a link that automatically logs into any user account associated with an order.
An attacker is limited to what users they can log in as due to the fact that it is only possible to login as a user with an order. Considering the requirement of an order, in most cases an attacker will only be able to log in as a customer-level user. However, it is common for shop managers or administrators to create test orders in order to verify order functionality. In these cases there is a chance that by exploiting the authentication bypass vulnerability, an attacker can gain access to an administrative user account, or another higher-level user account.
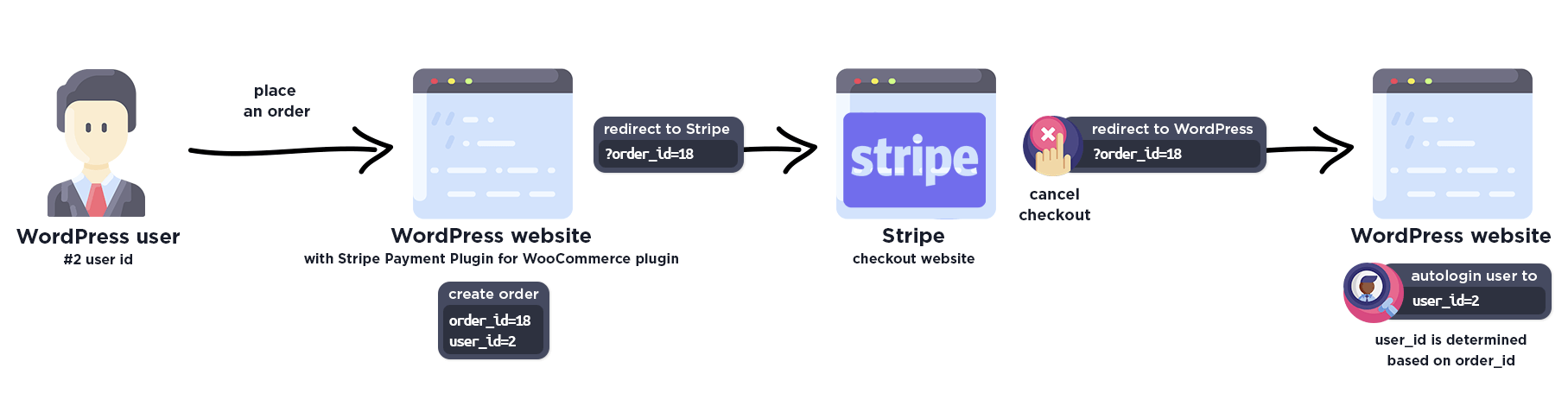
The normal order process looks like this:
The exploit process looks like this:
Disclosure Timeline
June 8, 2023 – Discovery of the Authentication Bypass vulnerability in Stripe Payment Plugin for WooCommerce.
June 8, 2023 – We initiate contact with the plugin vendor asking that they confirm the inbox for handling the discussion.
June 9, 2023 – The vendor confirms the inbox for handling the discussion.
June 9, 2023 – We send over the full disclosure details. The vendor acknowledges the report and begins working on a fix.
June 13, 2023 – A fully patched version of the plugin, 3.7.8, is released.
June 19, 2023 – Wordfence Premium, Care, and Response users receive a firewall rule to provide protection against any exploits that may target this vulnerability. Note that we delayed the firewall rule to prevent completely breaking the plugin’s core functionality as it was not being actively exploited.
July 19, 2023 – Wordfence Free users receive the same protection.
Conclusion
In this blog post, we have detailed an Authentication Bypass vulnerability within the Stripe Payment Plugin for WooCommerce plugin affecting versions 3.7.7 and earlier. This vulnerability allows threat actors to bypass authentication and gain access to the accounts of users who have orders. The vulnerability has been fully addressed in version 3.7.8 of the plugin.
We encourage WordPress users to verify that their sites are updated to the latest patched version of Stripe Payment Plugin for WooCommerce.
Wordfence Premium, Wordfence Care, and Wordfence Response users received a firewall rule to protect against any exploits targeting this vulnerability on June 19, 2023. Sites still using the free version of Wordfence will receive the same protection on July 19, 2023.
If you know someone who uses this plugin on their site, we recommend sharing this advisory with them to ensure their site remains secure, as this vulnerability poses a significant risk.
For security researchers looking to disclose vulnerabilities responsibly and obtain a CVE ID, you can submit your findings to Wordfence Intelligence and potentially earn a spot on our leaderboard.
Source: wordfence.com



